Getting Started with
GAT Labs
Learn how to get the most out of the GAT Labs Suite with practical guides and resources. Follow step-by-step articles on setup, configuration, workflows, security, and troubleshooting to confidently manage and protect your Google Workspace environment.
Table of contents

How to install GAT+
See Details
GAT+ is a Google Workspace Audit tool that by default can be installed only by the Super Admin of the Domain.
Install GAT+
How to install GAT+ Video
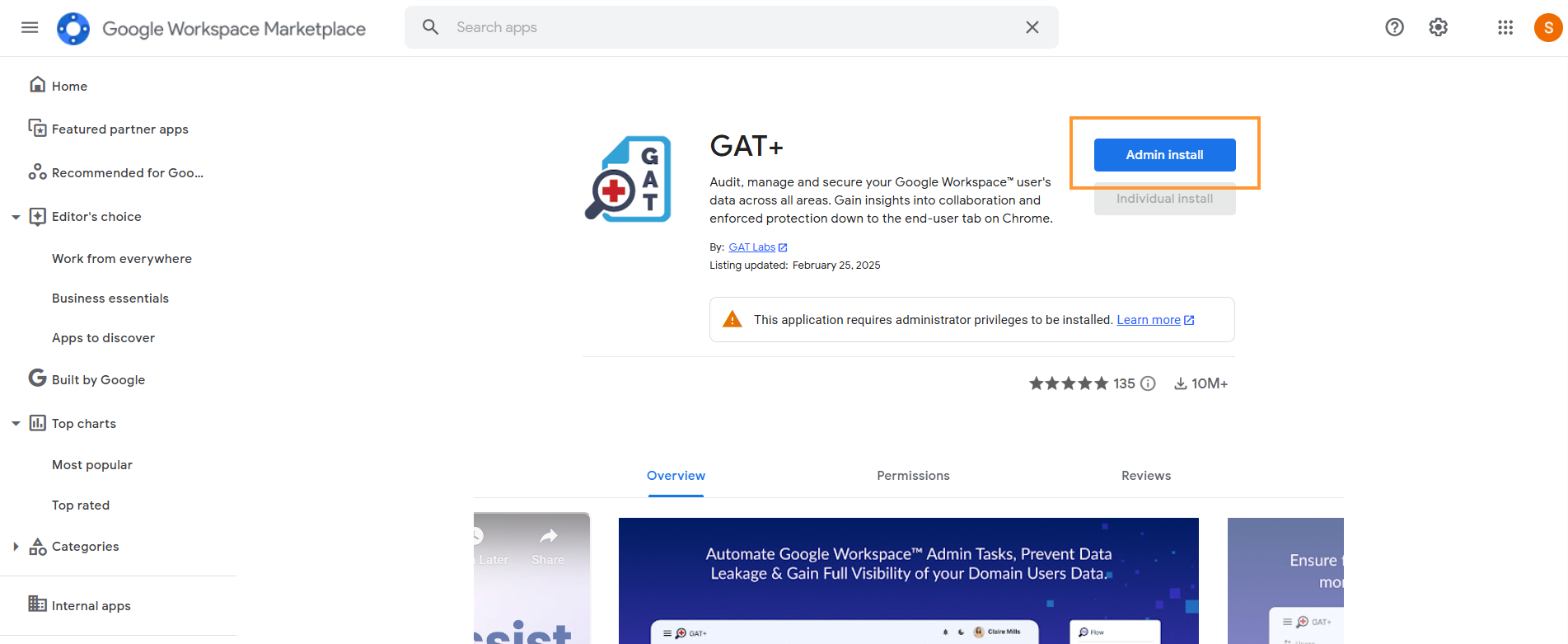
Step 1:
First login to your domain with Super Admin Account.
Navigate to > Google Workspace Marketplace > You can also search for GAT+ in the search bar.
When GAT+ is selected click on Admin install
A pop-up window will be displayed by clicking on “Continue“.
Then a new pop-up will be shown with all the permissions required.
Scroll down to the bottom.
- Under: Install the app automatically for the following users
- Select “Everyone at your organization”
- Note: installing on certain groups or org. units will not give clear and accurate data stats of the domain data
- Enable the checkmark – “I agree to the application’s terms…”
- Select “Everyone at your organization”
- Click on Finish
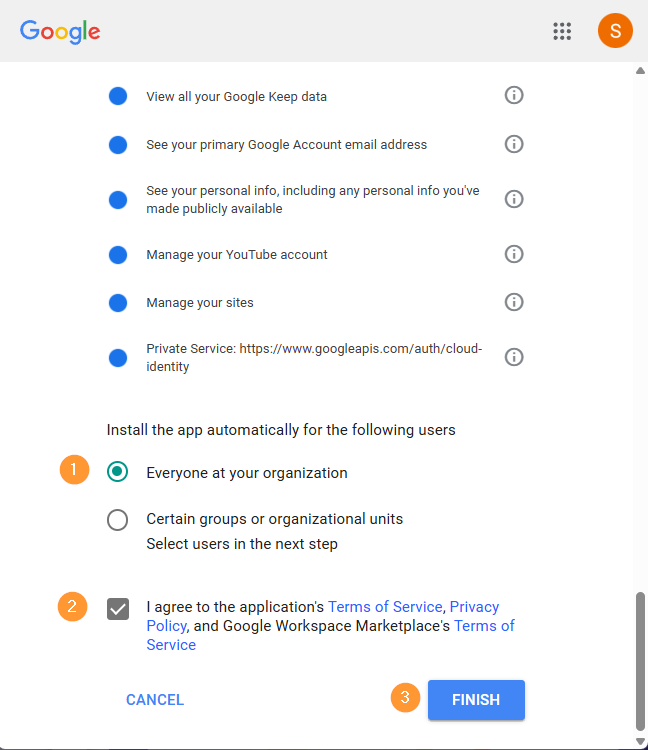
Note: You can not install it from an incognito window unless you are signed in to your Super Admin account.
Result
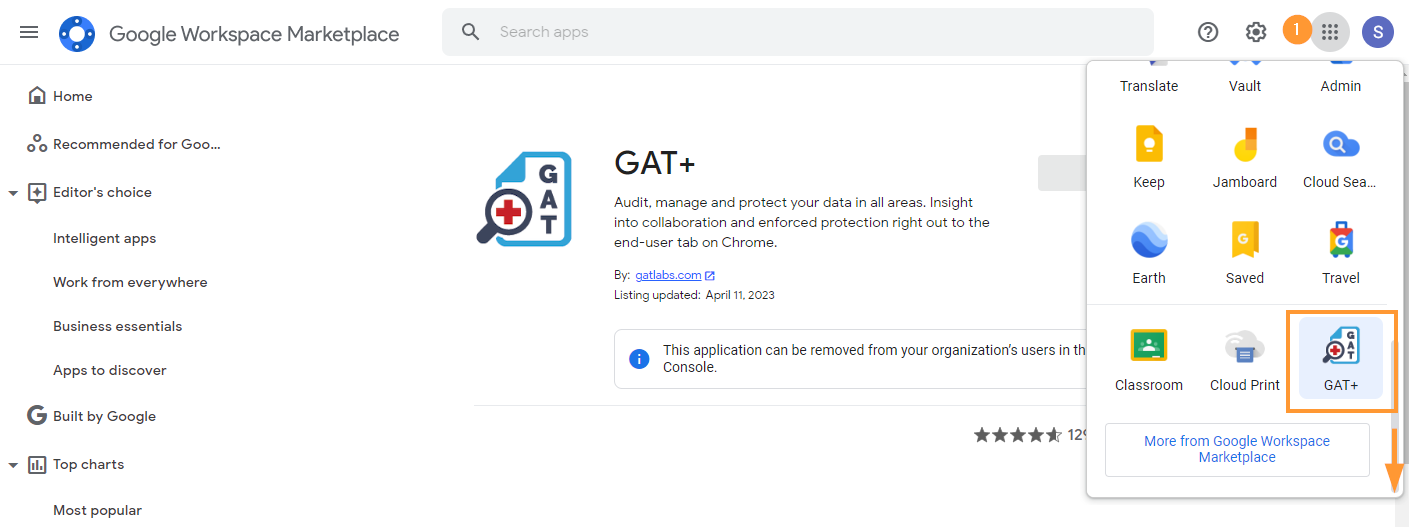
GAT+ will be installed.
When installed, click on the Goole apps button and scroll down to the GAT+ icon
Select Region
When you launch GAT+ for the first time you will have to select a region where data will be stored.
This selection is permanent.
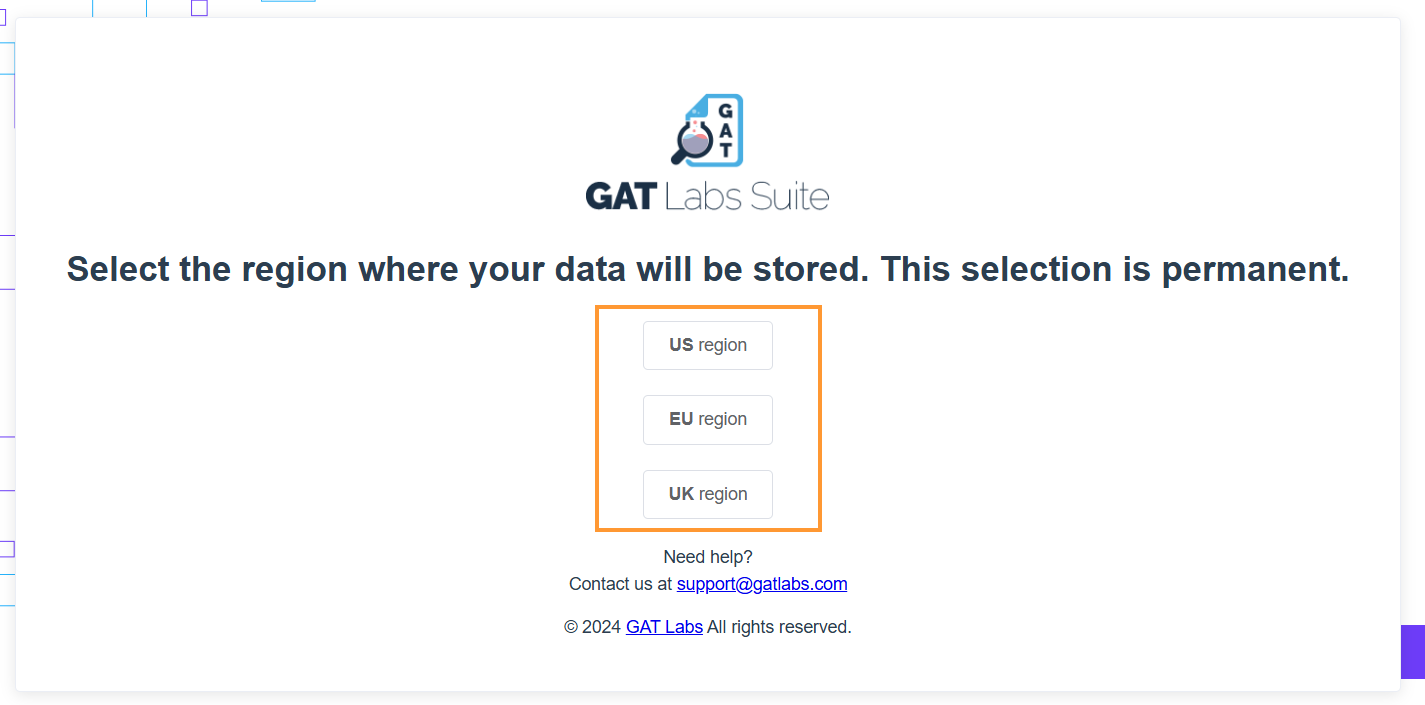
Select the Region where the data will be stored.
- US Region –
- EU Region –
- UK Region –
Once the region is selected GAT+ will be opened up for you.
This will be the initial login and the initial scan will be started.
The time for the initial scan to complete will depend on the size of the domain.
- The number of users
- The number of Drive files etc
Estimate time of the initial scan
We estimate the initial scan to take 30 min per 1 million files. When the scan is completed an automatic email will be sent to the Admin account.
Note: Subsequent scans will be faster.
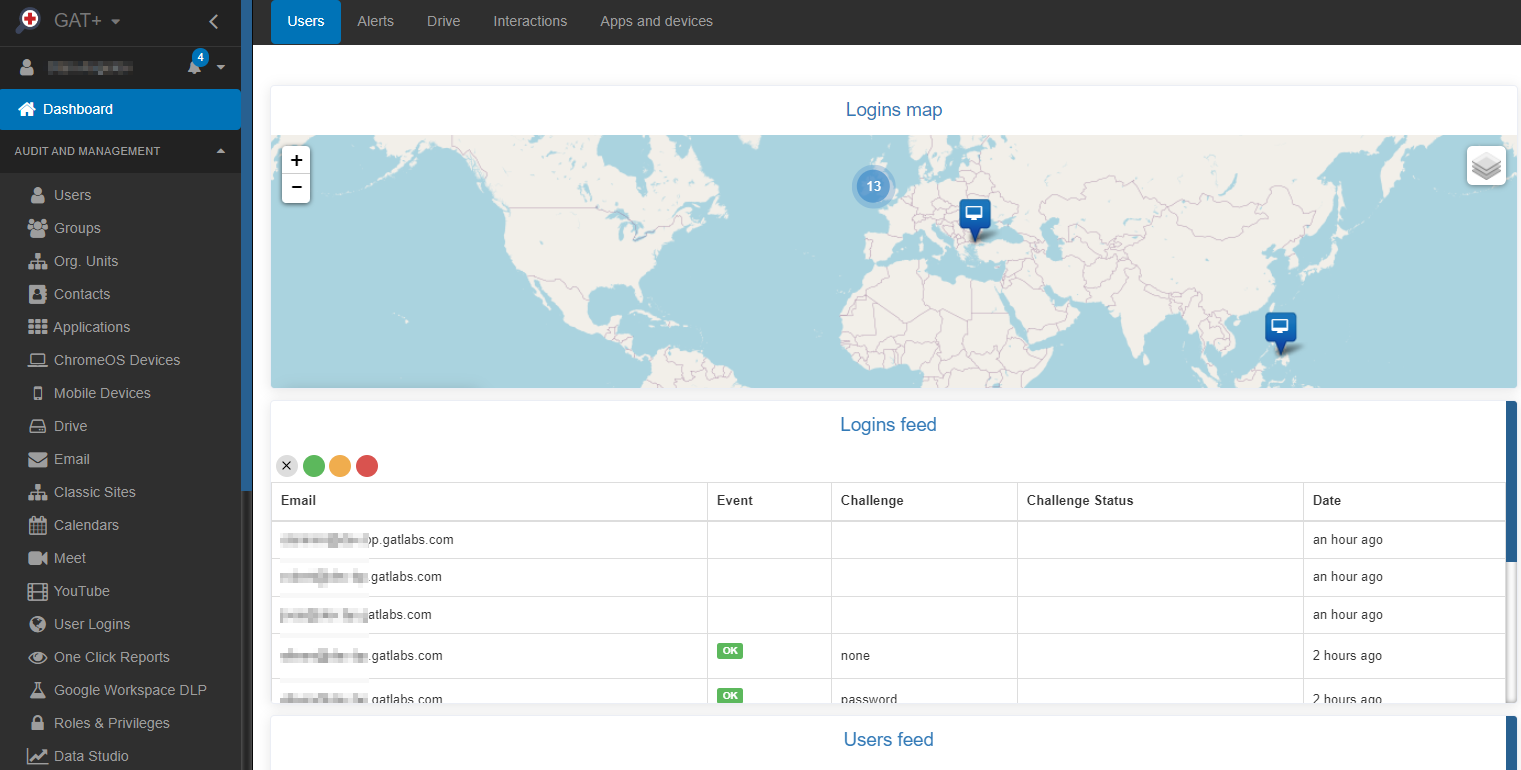
When the initial scan has been completed, the data from your domain will be displayed in the GAT+ console.
Data access
To view and access the full domain data (metadata), we recommend that GAT+ be installed domain-wide and all permissions be granted.
Access GAT+ by Super Admins only
By default, the tool can be accessed ONLY by Super Admins of the domain.
Non-admin accounts can see the GAT+ application under their Google Apps option, but CANNOT launch the tool itself.
When the tool is installed domain-wide, it can be launched from the Google Apps menu.
Click on the Google Apps menu button scroll down to third-party apps and click on GAT+

This will launch GAT+ into a new window on your browser.
Grant Access to GAT+ in Google Admin Console
See Details
Is GAT+ failing to run? Check these options in your Admin Console
How to make sure GAT+ is running correctly and showing correct information from your domain?
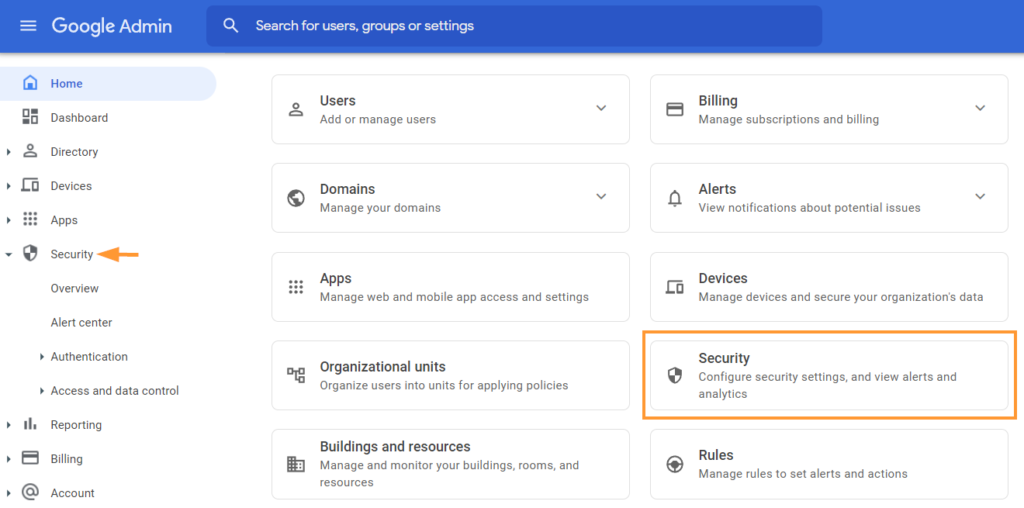
Navigate to the Google Admin console
Click the Google Apps menu button on the top right corner of your Chrome session and click on the Admin button

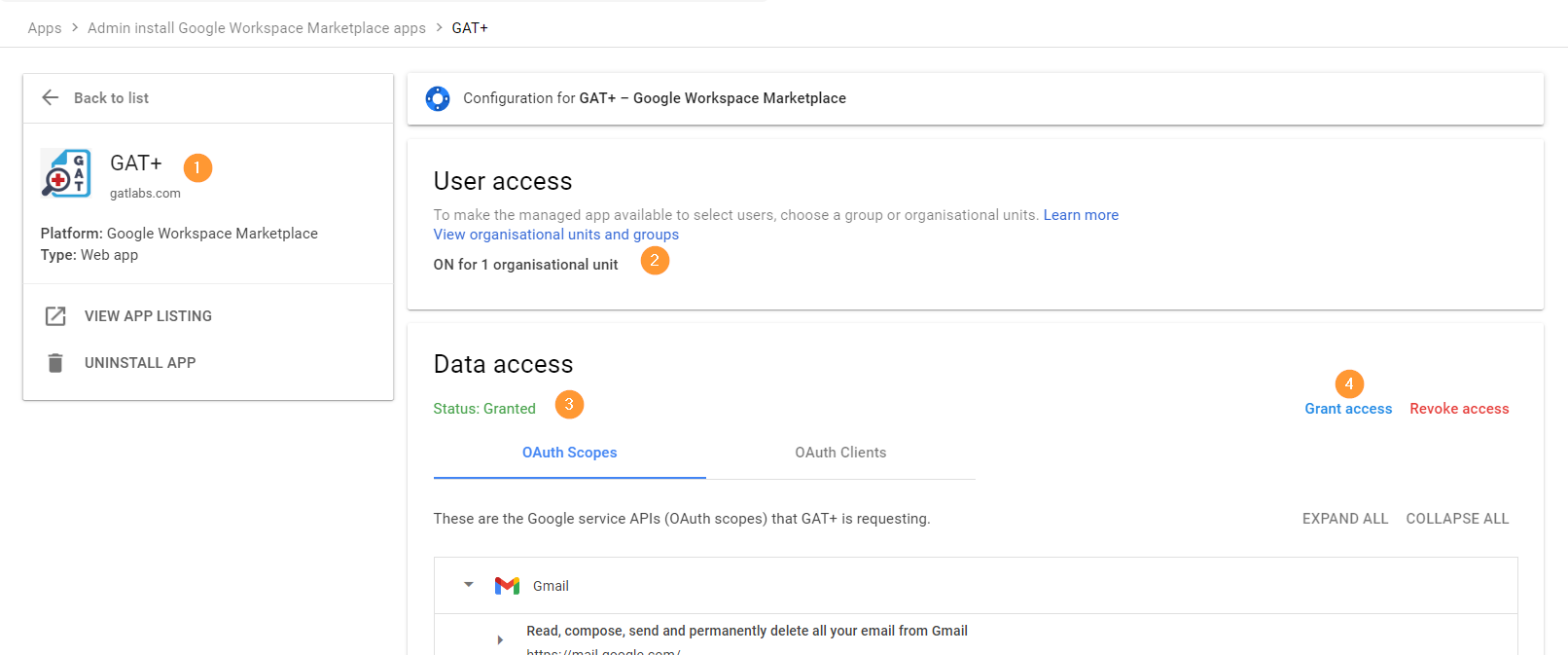
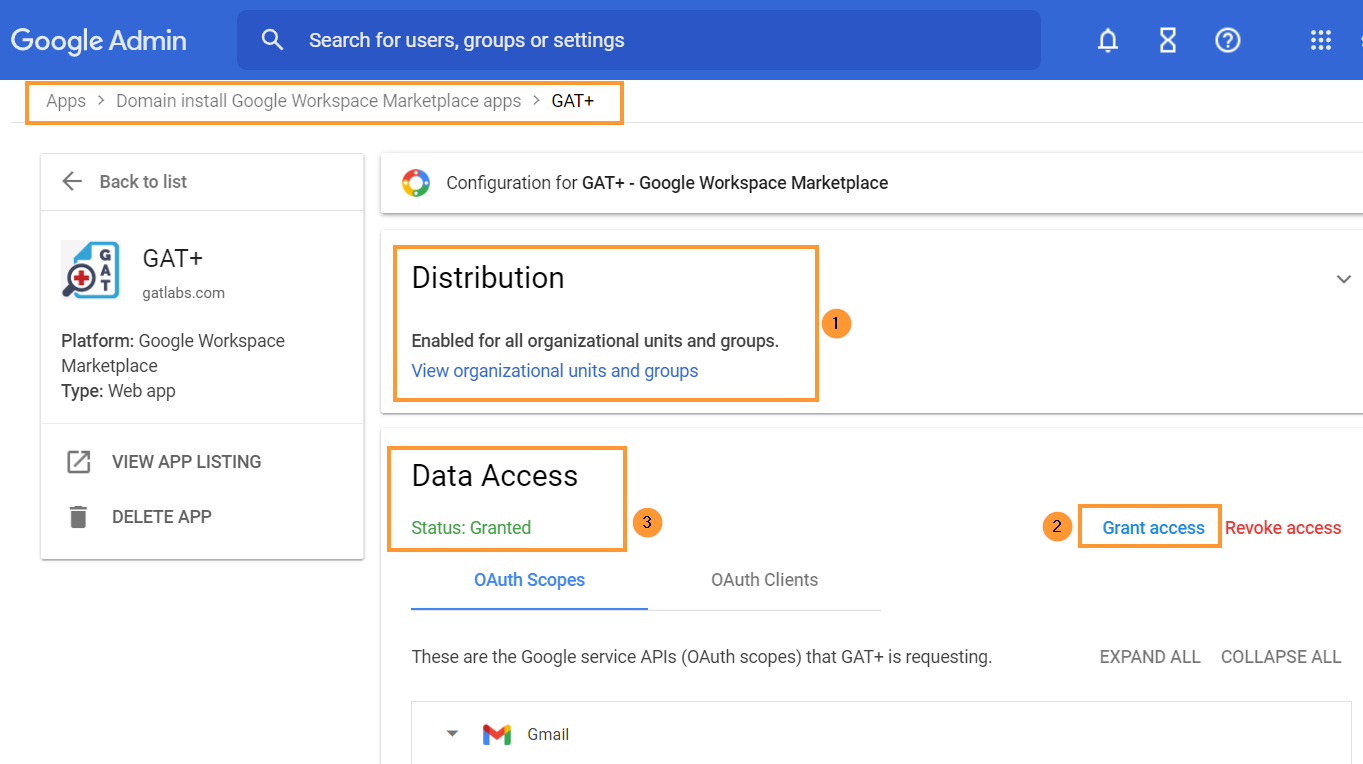
In the Google Admin console navigate to Apps > Google Workspace Marketplace apps > Apps list

Click on the GAT+ app
You will need to click and grant access to GAT+
- Distribution – it has to be Enabled for all organizational units and groups
- Data Access – status Granted
- Grant access – click to grant access to GAT+
IMPORTANT NOTE: As Google has deprecated their ‘Google Sites’ product, GAT cannot be granted access to that. You may see that the status is only ‘Partially Granted’ during this step. However, once you have clicked the ‘Grant access’ button you can consider this step finished.
Access by Super Admin Only
By default, the tool can be accessed ONLY by the domain’s super admins. Non-admin accounts cannot log in.
Context-Aware Access
If your domain has Context-Aware Access consider enabling and allowlisting GAT+.
Navigate to Security > Context-Aware Access > Assign access levels and enable the allowlist

Follow the steps required and explained by Google: https://support.google.com/a/

Navigate to Admin console > Security > Access and data control > API control > Manage third-party app access to Google services and then expand “configure new app”.
.
To enable Classroom auditing
Navigate to Apps > Google Workspace > Classroom > Data Access
Make sure that Classroom API – is turned on: ‘Users can authorize apps to access their Google Classroom data’

Troubleshooting GAT+ Initial Run Problems
See Details
Typically, these issues are straightforward to resolve. Don’t panic – fixing them is usually simple.
HAS A SUPER ADMIN FROM YOUR DOMAIN EVER USED GAT+?
To check if GAT+ is already installed click on your Google Apps button and navigate to the 3rd party apps section, you should see the GAT+ logo.

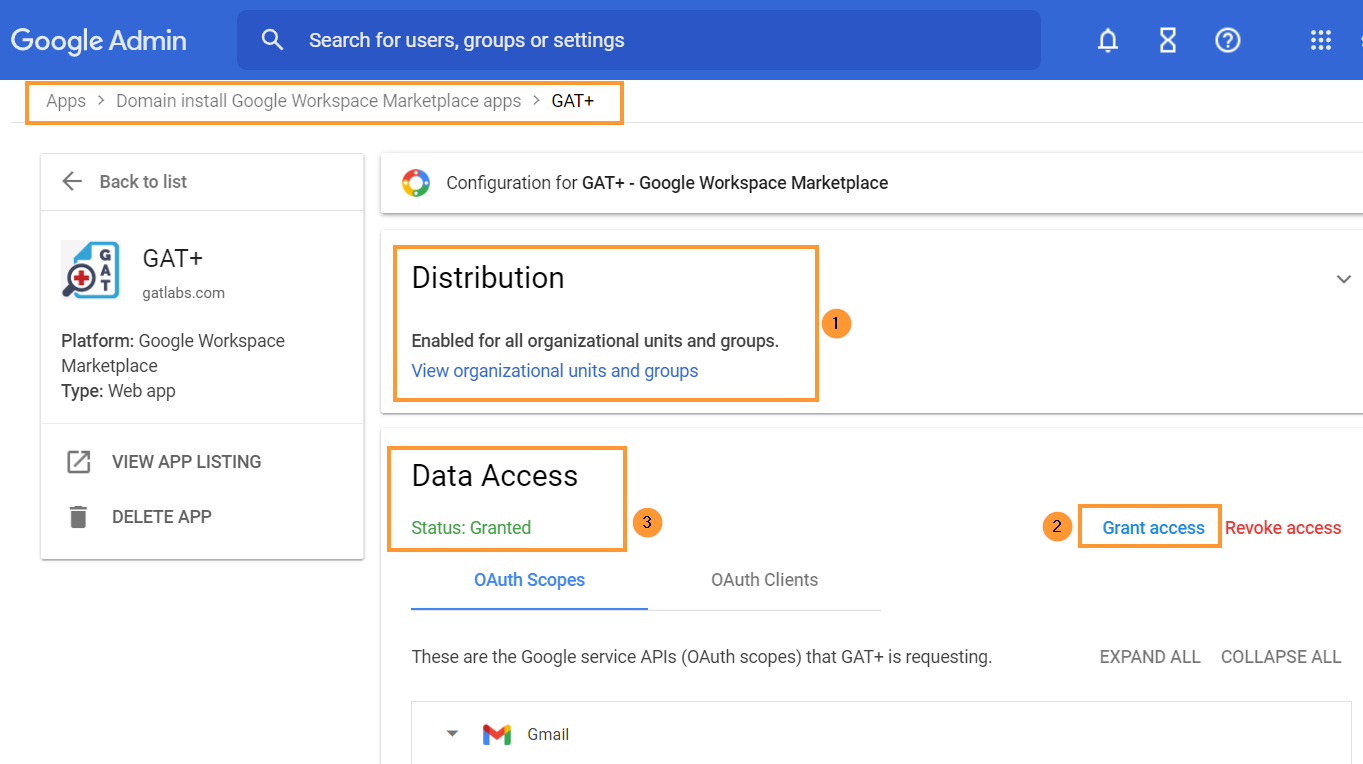
Alternatively, you can navigate to your Google Workspace Admin Console.
Navigate to Apps > Google Workspace Marketplace Apps > Apps list > GAT+
You will need to click and grant access to GAT+
- Distribution – it has to be Enabled for all organizational units and groups
- Data Access – status Granted
- Grant access – click to grant access to GAT+
Make sure it’s enabled for everyone and Data access is granted, this post will guide you through the process.
Still, having problems? do you need a fresh trial license?
IS YOUR DOMAIN TRYING GAT+ FOR THE FIRST TIME?
Navigate to the Google Workspace Marketplace the tool can only be installed by a Google Workspace Super Admin via the ADMIN INSTALL button.
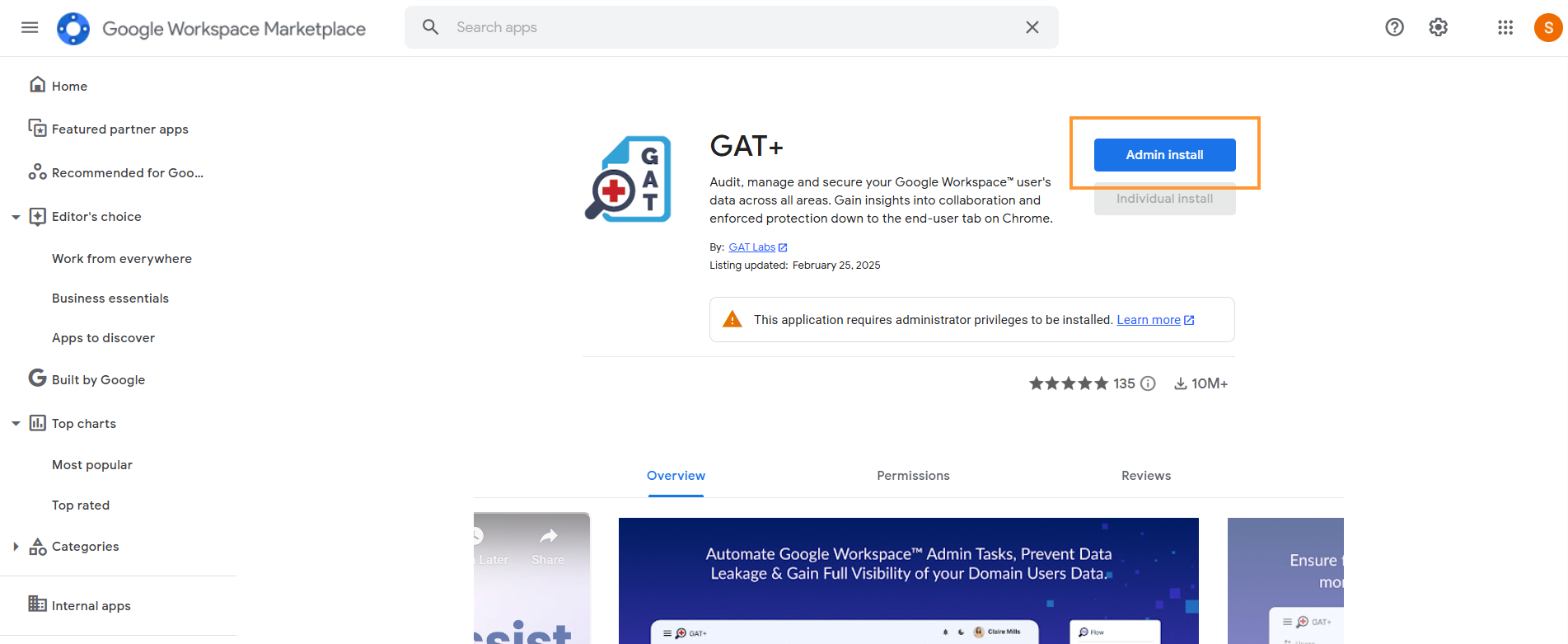
Remember, for addressing GAT+ Initial Run Problems, installation from an incognito window is not possible unless you’re logged into your Super Admin account.
Important Note: To ensure optimal functionality and avoid any GAT+ Initial Run Problems, install GAT+ in the root Organization Unit (marked as ‘On for Everyone’).
Access by Super Admin Only
By default, the tool can be accessed ONLY by Super Admins of the domain.
Non-admin accounts cannot log in to the tool.
Are Some Auditing Areas in GAT+ Empty?
To check this, go to the Security section in your Google Workspace Admin console.
Navigate to Apps > Google Workspace > click on Drive and Docs then click on Features and Applications
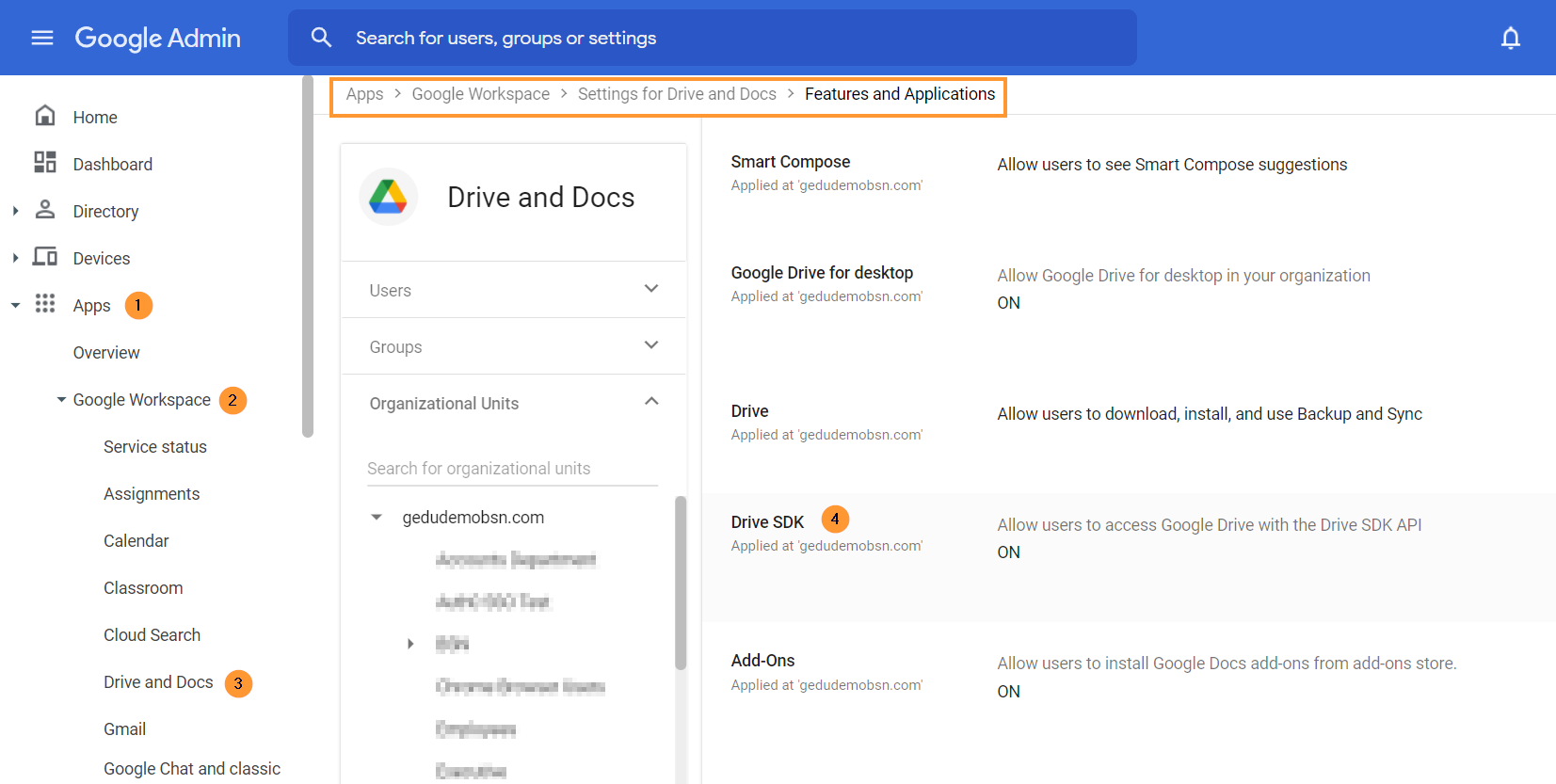
Select the root Org. Unit and make sure the Drive SDK is ON
PLANNING ON USING EMAIL DELEGATION WITH GAT UNLOCK?
You can use GAT Unlock to remotely set mail delegation for any user account.
As a Super Admin, you can give any user mail delegation access to another user’s account.
Navigate to Apps > Google Workspace > click on Gmail > then click on User settings
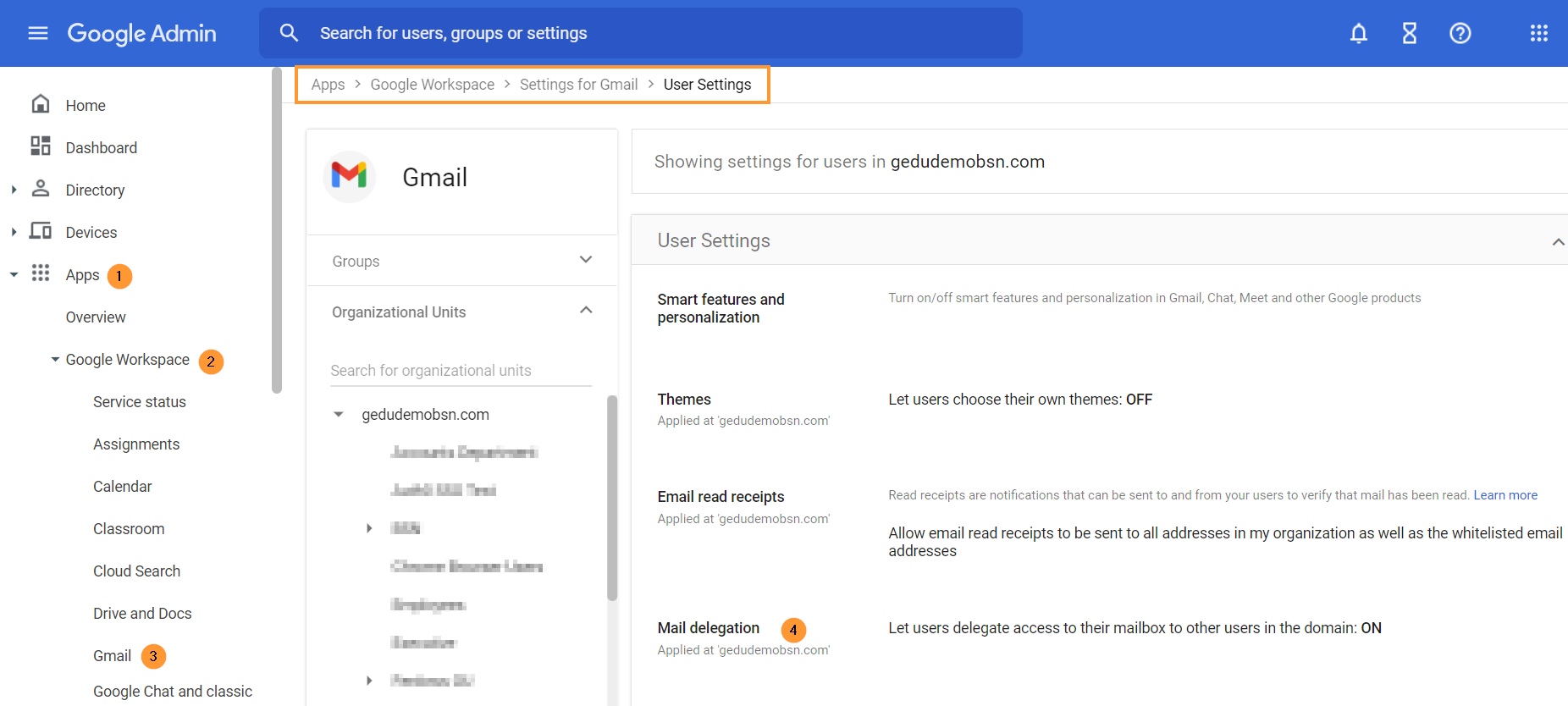
Turn ON the option to set Mail Delegation.
HAVE YOU ENABLED GOOGLE CLASSROOM AUDITING?
Navigate to Apps > Google Workspace > click on Classroom > then click on Data access

Click on to enable Classroom API then Save
Accessing GAT labs Suite of Tools
See Details
 Once you are in GAT+ to access other tools click on the GAT+ logo at the top left corner.
Once you are in GAT+ to access other tools click on the GAT+ logo at the top left corner.
 Each tool will be opened on a new browser tab.
Each tool will be opened on a new browser tab. Configuring your User Profile Settings and Preferences
See Details
Each Google Workspace Super Admin or Delegated Auditor within GAT+ can have their own user profile settings and preferences configured.
Configuring Settings
To configure your settings, navigate to GAT+, and click on your user name at the top right corner of the side menu.

Within the Settings area, you will see the Common, Querying, and Impersonation tabs.
Common
- Change Timezone – set up timezone
- Import/Export date format – select date format for exports
- UI date format – select the date format to be shown in the UI
- View the format preview
- Records Shown per page
Querying – Timeout settings
- General time-out settings
- Drive audit time-out setting
- Gmail/Email audit time-out setting
The above settings influence the waiting time for filter searches within the Drive or Email sections. A time-out error will be shown if time expires while waiting for a search to complete.
Impersonation – Multi-tenancy management for GAT+ Admins
- Multi-tenancy management for GAT+ Admins – GAT+ empowers Admins to manage multiple domains within a single account seamlessly.
- This new Multi-Tenancy Management feature streamlines administration by allowing one Admin to oversee various external domains effortlessly.
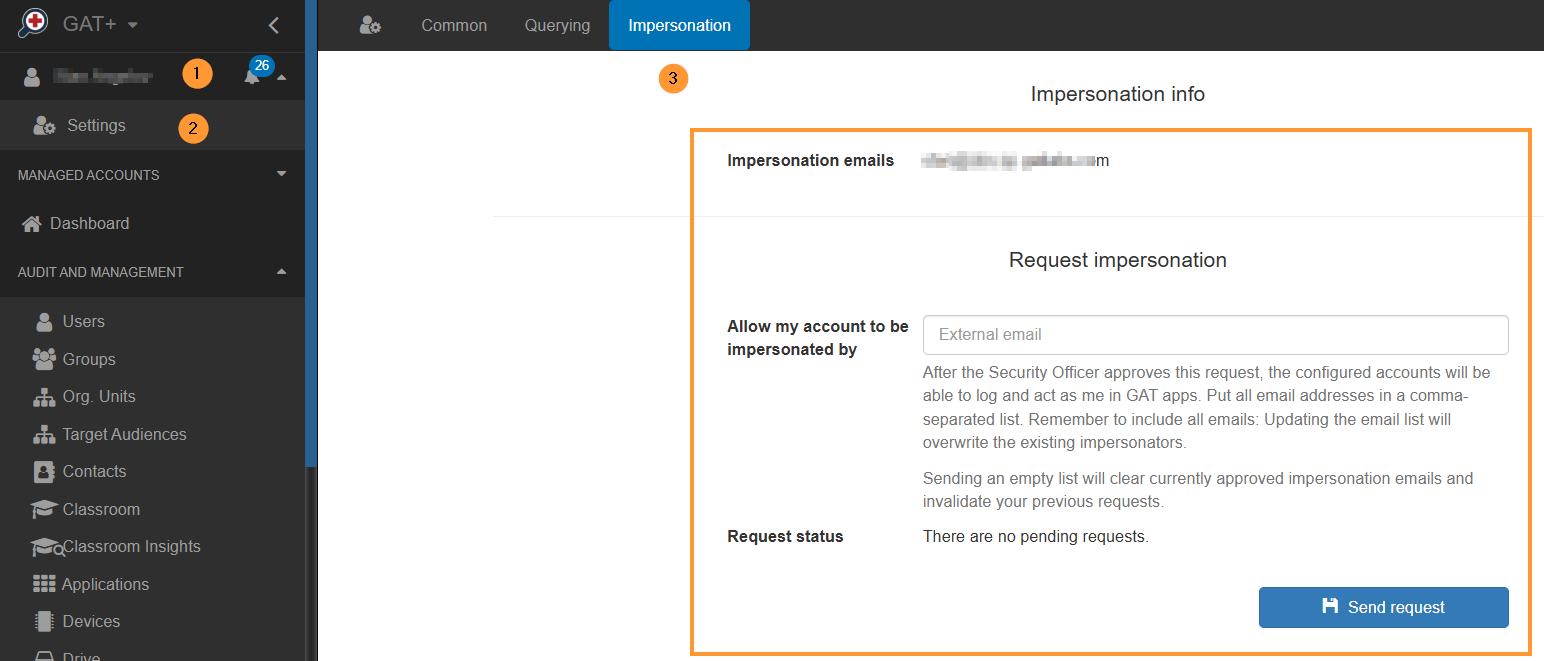
Here’s how it works:
- Centralized Control:
- A single Admin account serves as the central hub for managing multiple domains.
- Simplified navigation and oversight for efficient administration.
- Manager Account Access:
- Admins of individual domains grant access to Manager accounts for GAT+ control.
- Collaborate seamlessly with managers without compromising security.
- Impersonation Feature:
- External users cannot access a domain unless are granted permission by the Admin using the Impersonation feature.
- Ensures secure and controlled access to domain-specific functionalities.
This streamlined Multi-Tenancy Management feature in GAT+ enhances efficiency, security, and collaboration for Admins overseeing diverse domains.
Experience the ease of unified administration with GAT+.
More information can be found here.
Drive Clean Up – Duplicated files shared out
See Details
GAT+ audit tool can help admins identify files using all sorts of criteria using the ‘Filtering‘ feature available throughout every audit.
In this example, we are looking to identify all of the video files that are duplicated and shared with external users and then manage their access and ownership.
The scenario is to find the duplicate files, remove the external shares, and then delete the duplicate files.
To achieve this, we can break down the task into steps.
Step 1. Identify duplicated video files that are shared externally
Starting the Drive Clean Up:
- First, navigate to the Drive audit (1)
- And then to the Files tab (2).
- Next, run the filter to find files, select the filter icon (3).
- Now the filter needs to be defined, select the Type to be Duplicated Files. (4)
- Select the minimum number of duplicates you are looking for, so ideally this is 2 and cannot be anything under, because at least 2 files are duplicates.(5)
- Now we can add more criteria to the definition of the filter to target the files we want.
- Select the field to be ‘Type’ (6)
- Select the type to be video (7)
- Add a rule to the rule definition block (8)
- Now we want to find these files that are externally shared, select the field to be ‘Sharing flags’ (9)
- Select the ‘Sharing flags’ to be ‘Shared out’ (10)
- Apply the filter (11)
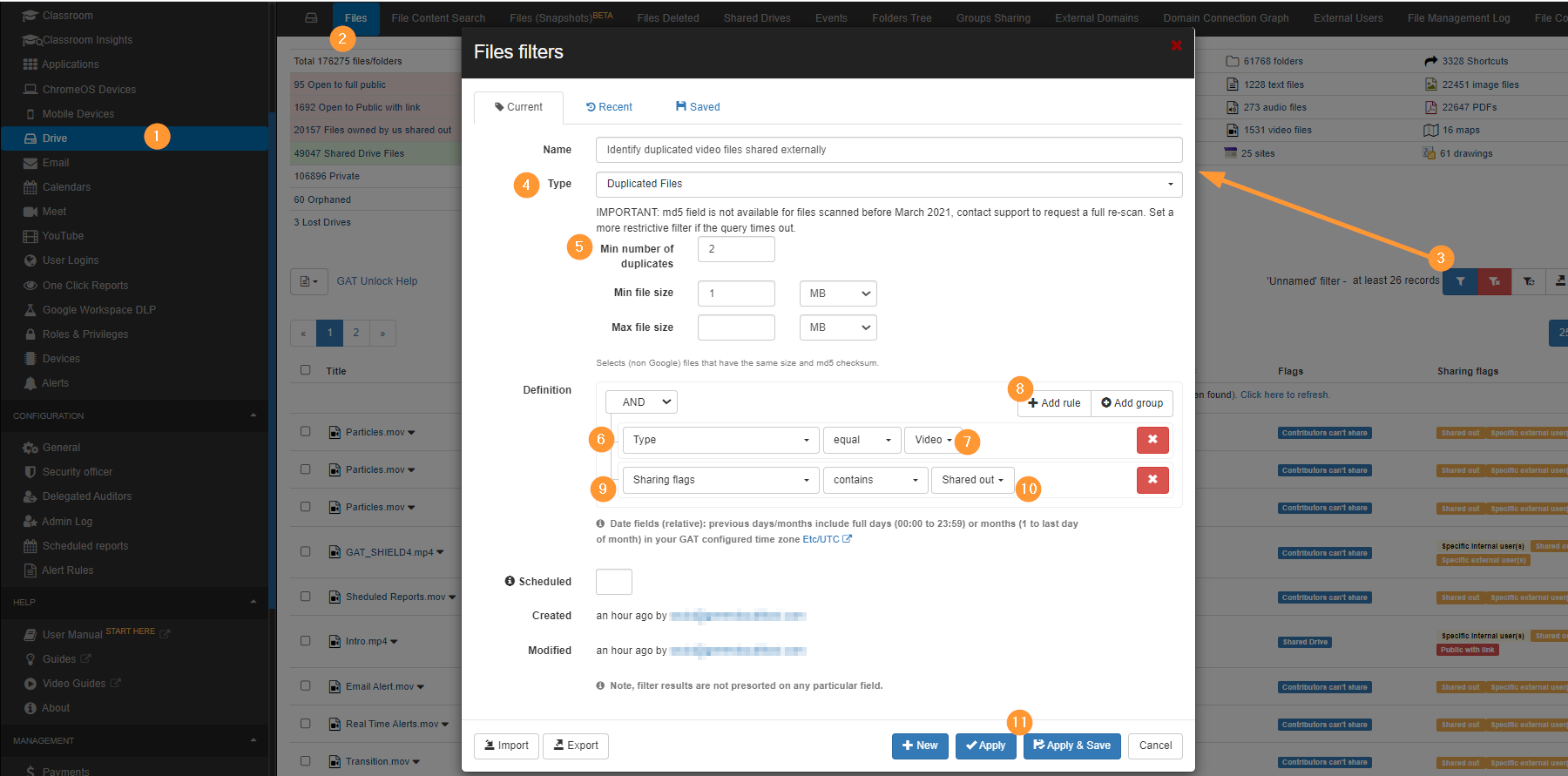
Result of filter
As a result, all the video files that are duplicates and shared externally will be displayed.

Shared Drive result
Some files might be part of Shared Drives, where you cannot change ownership, as Shared Drives do not have owners.
You can exclude Shared Drive files by adding a simple additional filter.
- Flags – “doesn’t contain” – Shared Drive

Step 2. Take action to change ownership and delete duplicates
As an Admin or Delegated auditor, you can now change the ownership of those files and then delete them from the Google Drive UI.
For example, remove the permissions of all external shares on the files and transfer ownership to delete the duplicate files.
- Select all files to be deleted and leave the copies you want to remain
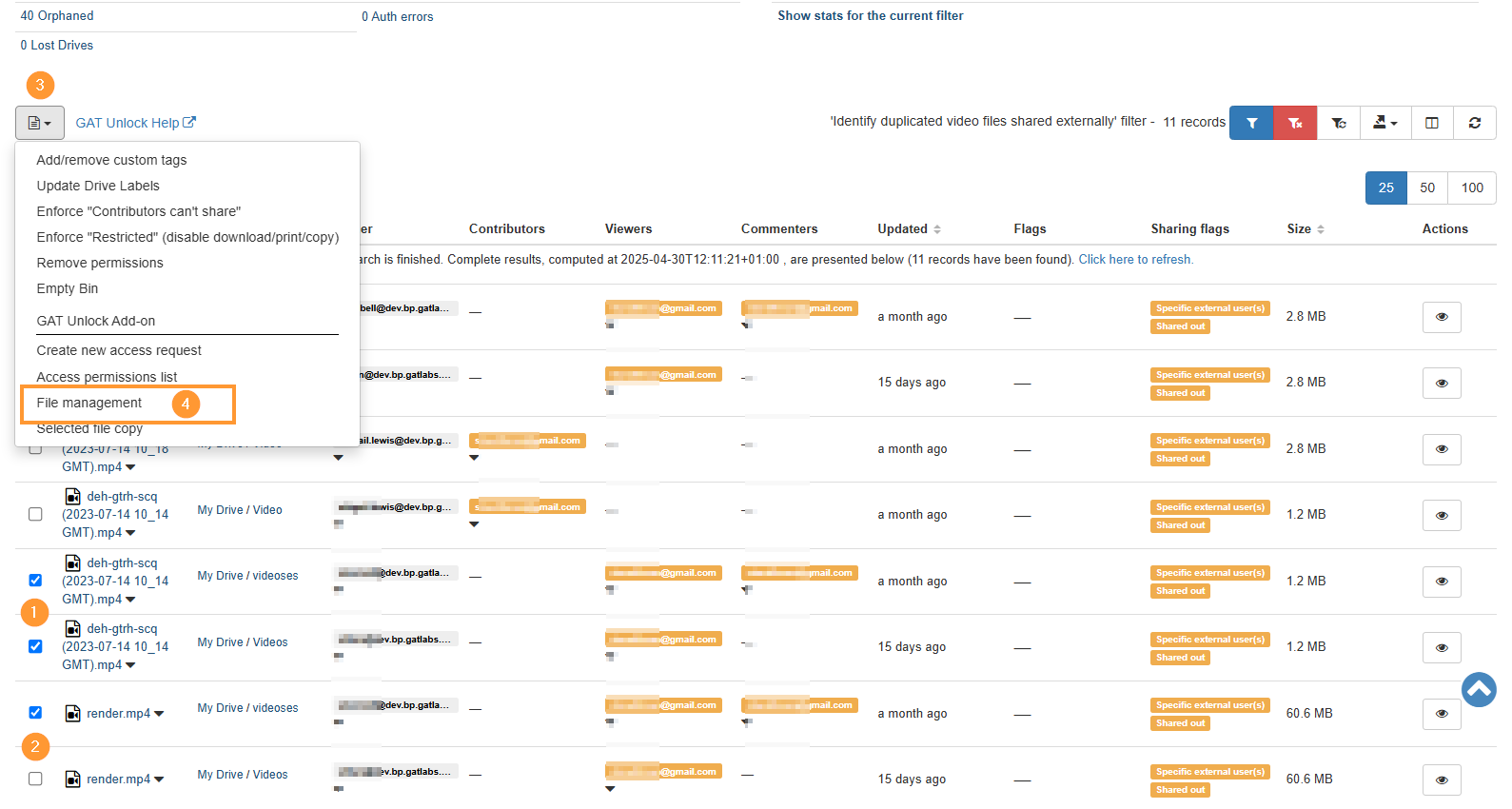
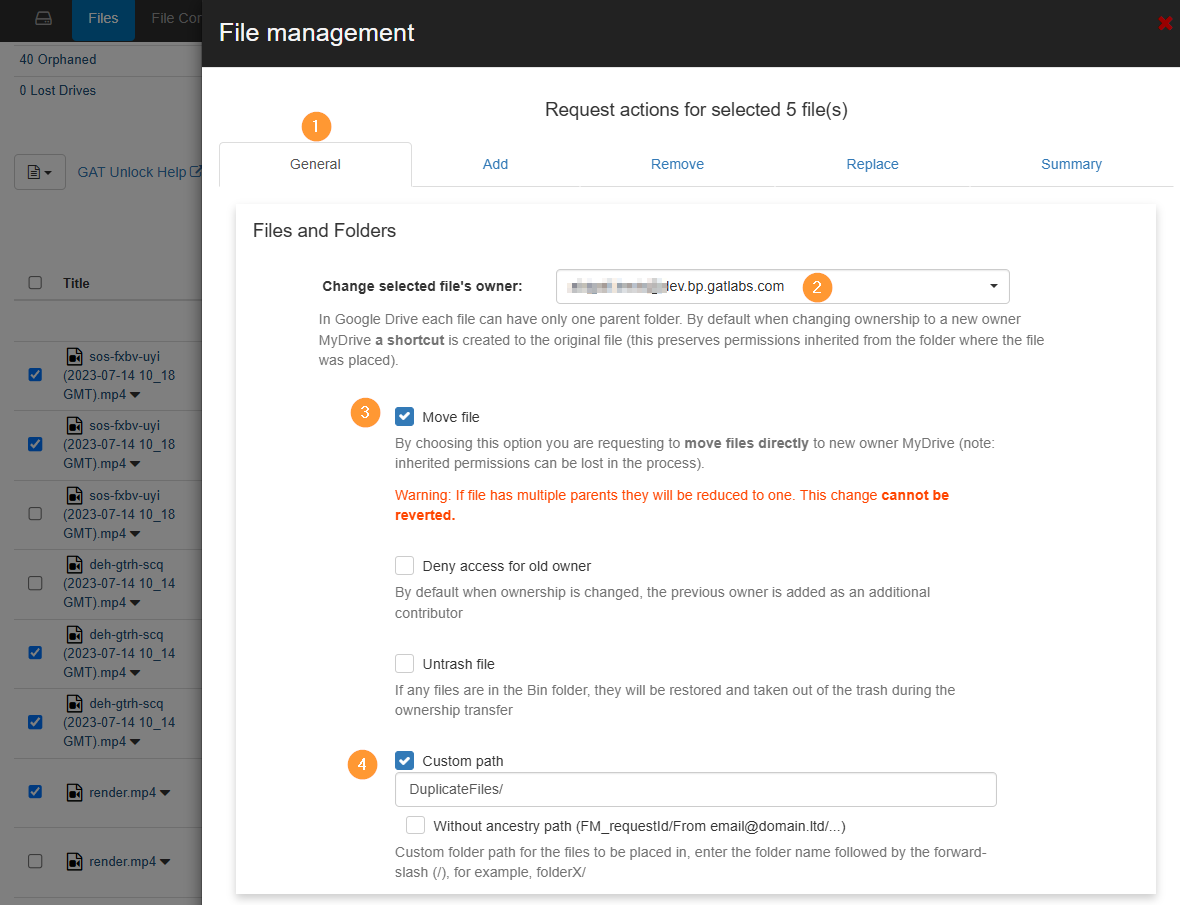
- Select ‘File management‘. This operation will allow us to change ownership of the files and remove their permissions in the same File management Job.
- A new window will be displayed with the actions that can be taken
- Fill in the details for the ownership change
- General –
- Change the selected files’ owner – enter the new owner’s email
- Move file – select to move the files directly, rather than creating shortcuts
- Custom path – select location where the files will be placed when ownership change occur
- General –
- Next, proceed to the ‘remove permissions‘ tab and choose the option to Remove all external permissions.
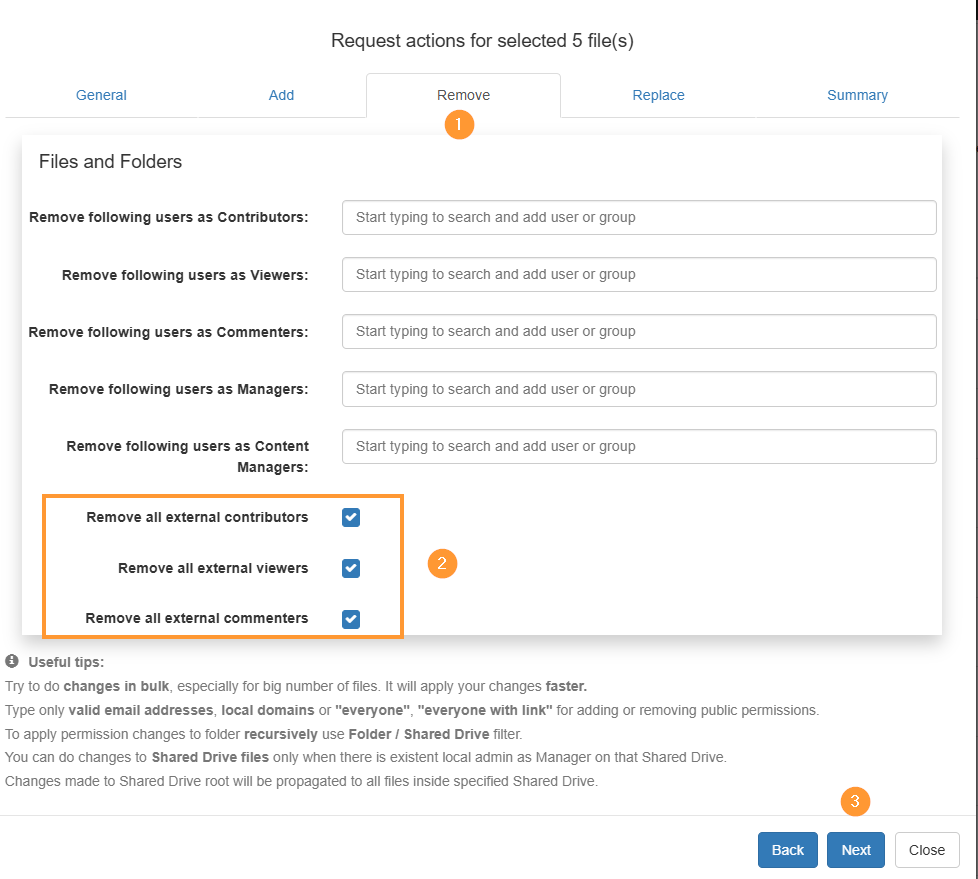
- Next, go to the summary tab and select ‘send request’

Approval of action
The security officer will receive an email to approve the Unlock request.
The email will lead them to GAT+ > Security Officer > File Management

Result in the File management log
When the job is finished, it’s possible to check the status of every file where action was taken by checking the job in the File Management Log tab in the Drive audit.

Step 3. Drive Clean Up- Delete duplicate files
When the change of ownership has finished, as part of the File management, we selected where the files will be located when the ownership change happens.
Because of the change, the files will be located in the new owner’s My Drive under the added folder.
From there, the new owner can delete the duplicate files.

Related Posts
How to find any duplicate files in Google Drive
Google Workspace Admin Best Practices in GAT Suite
See Details
Best Practices List
- Generate a monthly report on the extensions your employees are installing Chrome extensions audit
- Restrict users from downloading potentially malicious file types Report and remove file downloads
- Setting up alerts for when racial/homophobic language is used (and take a screenshot) Configuring settings for Alert Rules
- Categorize sites with tags so you can see at-a-glance if employees are working Auditing sites with browsing tags
- Set up an alert for when Two Factor Authentication is disabled Alert when 2FA is disabled for any reason
- Set up document tracking for docs containing sensitive data Track visitors and editors of specific documents
- Set up policies for applications allowed on the domain Policies for Google Workspace apps
- Create copies of externally owned files List all externally owned files
- Remove public access to files (automatically after being shared) Remove public and public-with-link permissions from Google Drive Files
- Remove files shares to personal accounts Find all files shared to Gmail accounts and remove them
- Monitoring User Logins Monitoring Google Cloud login behaviour
- Find out who’s missing their meetings Report when the Google Meet organiser is not present
- Set up alerts for Email Delegation Email delegation alert rule
- Set up alerts for new email filters Alert for new Gmail filter added
- Automate actions that will be taken when a user violates an alert Set up event workflows based on GAT+ alerts via GAT Flow
- Force users to change their passwords every 3 months (set as a recurring workflow to run automatically) Change users passwords at the next login in bulk
- Allow users access to shared drives and sensitive folders automatically, only when 2FA has been enabled (and remove access if 2FA is disabled) Run workflows based on 2FA change
- Remove email filters regularly (automatically) Remove users email filters in bulk
- Configure a set of actions to do when offboarding users (transfer files, remove app tokens, set Out of Office reply) Actions available when offboarding users
- Deploy the GAT Shield extension to everyone in your organization Deploy GAT Shield
FAQ’s – GAT+ Features not available based on Google plan
See Details
GAT+ is a third-party Google Workspace app — It offers Super Admins powerful Google Workspace auditing and reporting for their domain.
What Google Plans are covered by GAT+?
By default GAT+ audit covers every Google Workspace plan.
Features not available based on the Google plan
The only feature that is not available in GAT+ based on Google plans is the Drive Events.
The Drive Events feature is not available for Google’s most basic plans – Business Starter and Education Fundamentals.
The Drive Events (Drive Log Events) are supported in:
- Business Standard
- Business Plus
- Enterprise
- Education Standard
- Teaching and Learning Upgrade
- Education Plus

Why are Drive Events not available?
This audit is not available because Google does not report on those events and therefore GAT+ cannot report them either.
More information can be found on Google’s end here.

GAT Unlock – First Steps
See Details
What is GAT Unlock?
GAT Unlock is a Multi-Party Approval system for Google Workspace that controls access to sensitive data and high-risk admin actions.
It is designed so that actions such as accessing documents, viewing email content, or changing file ownership cannot be performed by a single admin alone. Every request requires approval from a second authorised role, typically a designated Security Officer or Verification Officer, formally approved within the organisation.
GAT Unlock is an additional service available across the GAT suite. For non-Education domains, it is offered as a paid add-on. It is not enabled by default and cannot be self-configured, ensuring activation and access are tightly controlled from the start.
Policy
Due to security reasons, we do not enable GAT Unlock during the trial version of the app.
From the introduction, the service will be visible to domains and each domain Admin can apply to have it enabled. To avail of this service please email unlock@generalaudittool.com with your request. The requesting email must contain the following 4 items.
- The contact details of the Google Apps Administrator applying.
- The name of the Security Officer(s), her/his position(s), email and phone number.
- The contact details (email and phone number) for the person from whom the GAT team must seek confirmation before enabling this feature (See the list below for the minimum level of organization officer we expect to have to request approval from. Please send us their full contact details also and inform them they may receive contact from us.) This is required to verify the separate identities of both the Administrators and Security Officers.
- The PO details for the requested service, see the price list below. (Not required for education domains that have purchased GAT.)
There can be many Security Officers, and the service will be available to all Super Admins once enabled.
| Number of users in the domain | Verification Requirements or job position to approve the enablement of the product |
| 1- 49 | Owner, CEO, CFO |
| 50 – 99 | CEO, CFO, Head of HR, CIO |
| 100 – 499 | CEO, CFO, Head of HR, CIO |
| 500 – 999 | CFO, Head of HR, CIO |
| 1,000 – 4,999 | Head of HR, CIO, CSO |
| 5,000 – 9,999 | Head of HR, CIO, CSO |
| 10,000+ | Head of HR, CIO, CSO |
You can add as many Security Officers as needed, all of them will receive the Super Admins or delegated auditors requests and any of the designated Security Officers will be able to approve or deny.
The Security Officer list for all domains is maintained by generalaudittool.com staff. Only Security Officers and Approvers can request changes to the list via unlock@generalaudittool.com
When the ‘GAT Unlock’ service is enabled Administrators can generate access or change requests, but only Security Officers can approve them. An individual can be a member of both lists but cannot approve their own requests. Only a Super Admin or delegated auditor can request permission to change files/folders or access to contents. The Security Officer’s sole purpose is to approve requests sent.
By design a Security Officer cannot self approve their own requests, you would need a second Security Officer to perform changes.
For easier management, it is recommended to have at least two Security Officers in the domain.
Administrators and Security Officers should remember the verification process is there to protect you, your domain data and your user’s privacy and rights, while also enabling you to act in the organization’s best interests.
Why all this effort?
We really respect your data security. We respect your company’s right to be protected. This is the highest security model available within Google for the Work Environment.
How to Use GAT Unlock
File Management – Changing ownership or file access rights
GAT Unlock is tightly integrated with the powerful search and filter options available in GAT+. This means you only have to do things once.
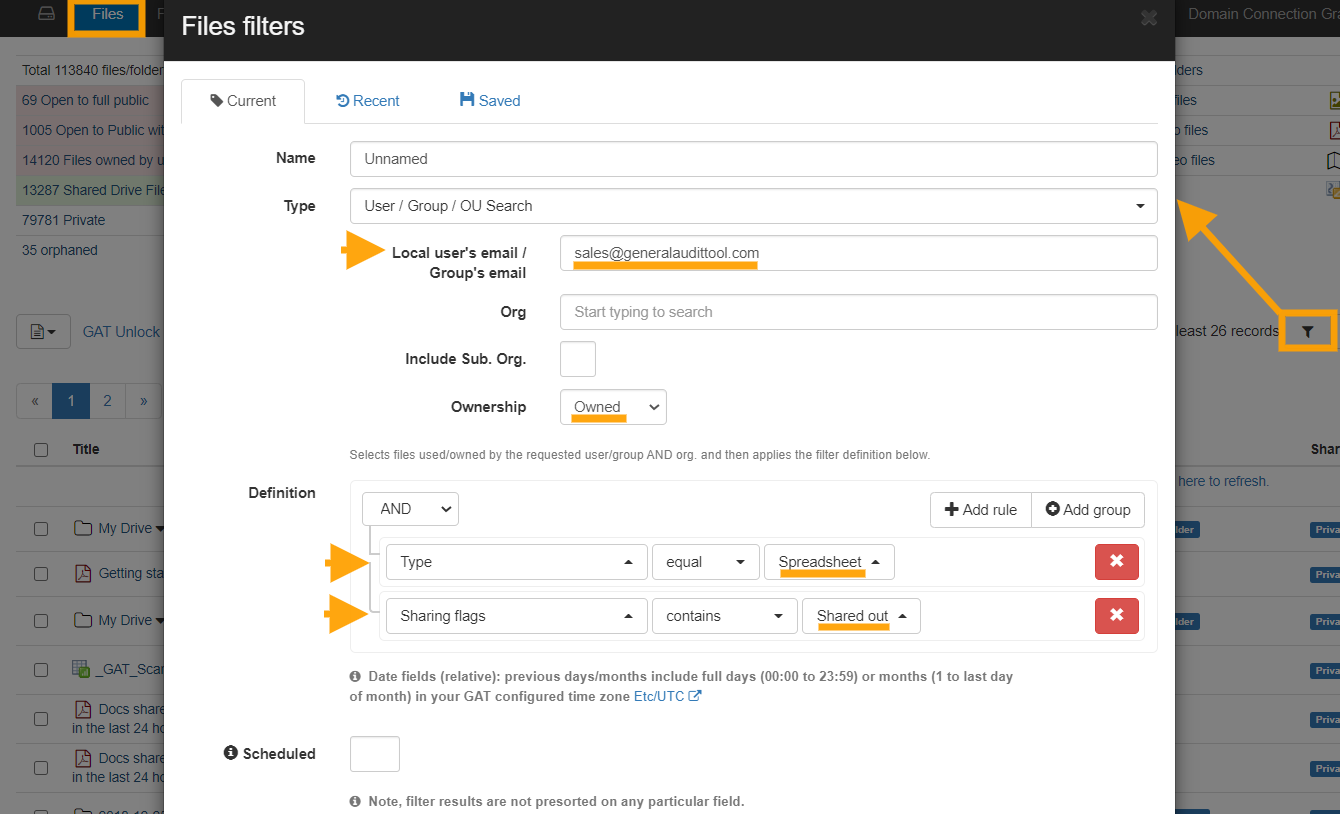
In this example we are going to find all the spreadsheets owned by the group ‘sales’ that are shared externally, then we will remove the external sharing and change the ownership (on all the selected files at once).
💡 TIP: Always narrow the file request with a search first, saving time and simplifying approval.
Step 1: Click on the ‘Apply custom filter’ button in Drive Audit.
Select the following option:
- For the filter Type select User/Group/OU search, we will enter the ‘Sales’ group in this field ‘Local User/Group’, make sure to enter the full email address.
- Under the Ownership option select ‘Owned’, this will show all the files owned by the ‘Sales’ group. Otherwise, it would show all of the files associated with the ‘Sales’ group, were Sales shows up as Owner, Editor or Reader.
- In the filter Definition area, select the parameter Type equal to Spreadsheets and to add another search parameter click on the ‘Add rule’ button and select ‘Sharing Flag’ contains ‘Shared Out’. Selecting shared out will only focus on files leaving your domain.
Step 2: Next select the Files you want to act upon, clicking beside ‘Title’ will select all files from the search, or you can select individual files, by clicking beside the files. Click on the button File operation and then select the File Management option. NOTE: The transfer will work on both Active and Suspended accounts.
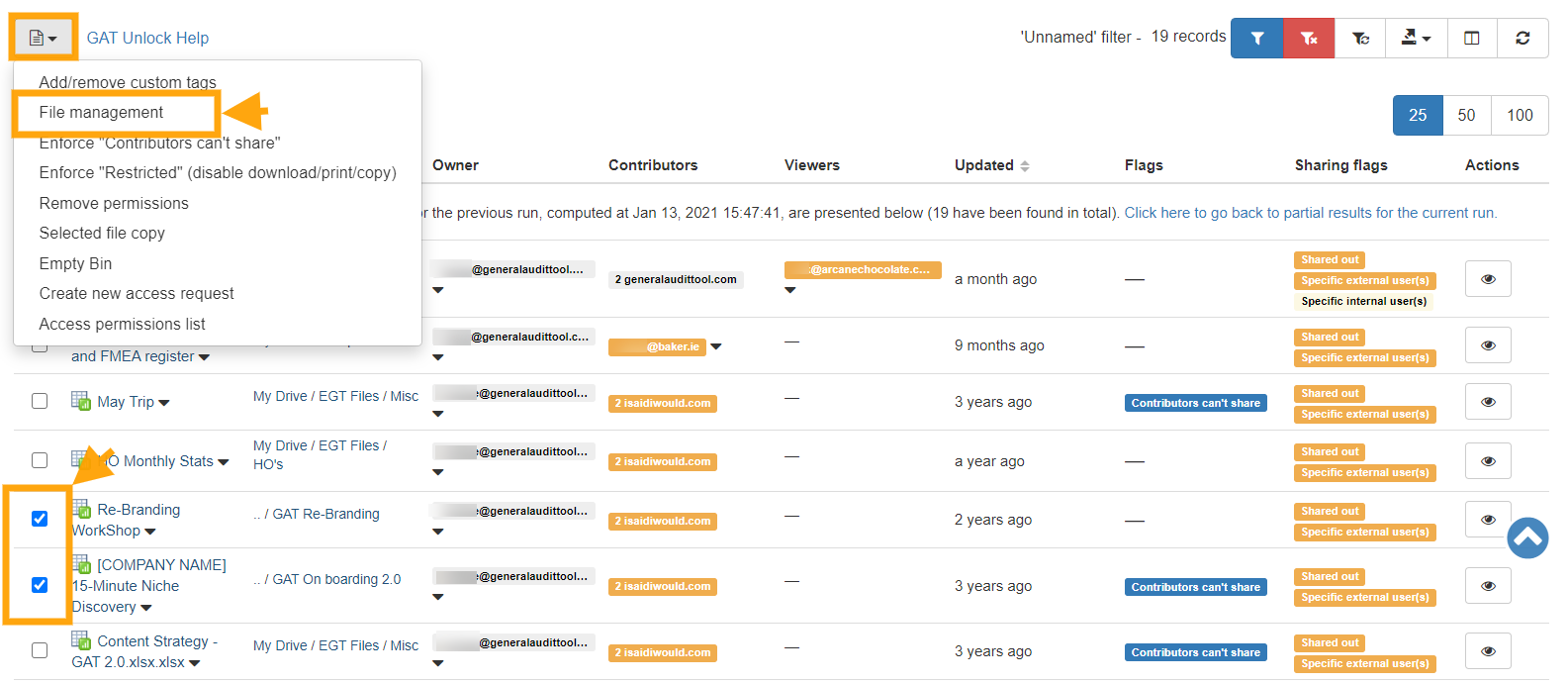
Step 3: In this example, we are making the account manager the new owner of the selected files.
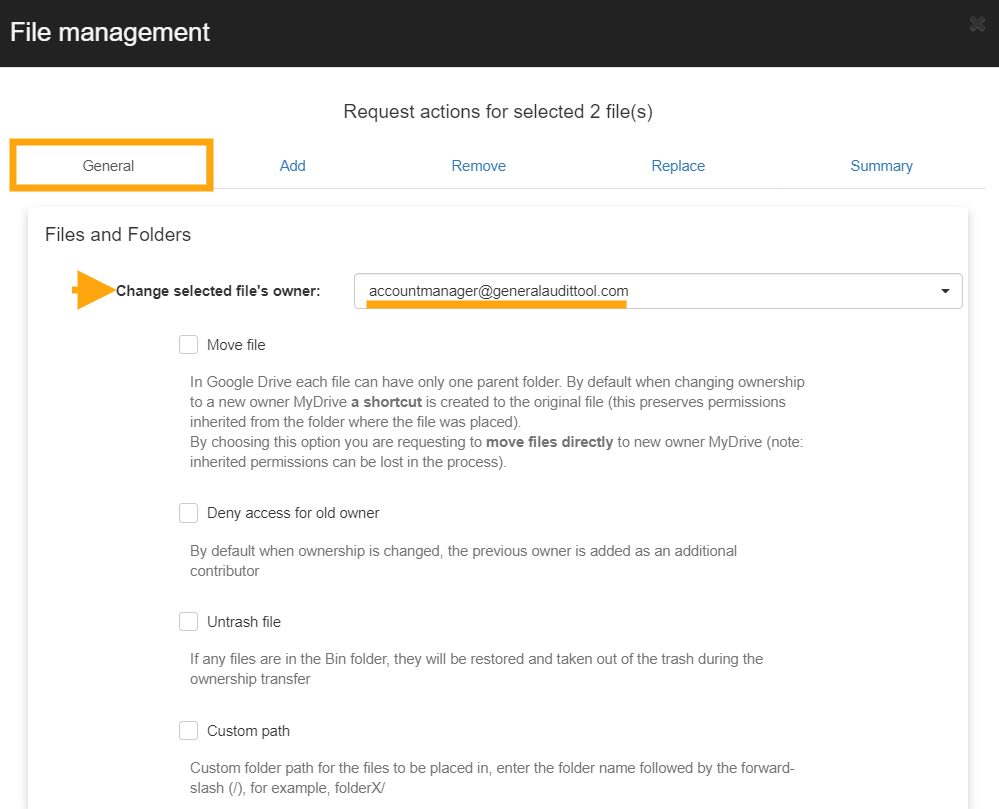
We can also remove external access to the spreadsheets and add or replace the sharing permissions.


Then click on Send request.
An email is going to be sent to your security officer. Click here to see and approve the request.

If the security officer approves your actions, they will be executed and you will be notified.
If permission is not granted by the security officer, you will also be notified and no actions will be taken.
Access Permissions Granted – How to Silently Copy or View Files
We are going to use a powerful search feature inside of the GAT+ Drive audit to identify the contents of the documents we’re going to investigate. This feature is called the ‘Full content text search’. It allows admins/delegated auditors to use a word or sentence to search through all of the files across the domain and to return documents that contain them.
Step 1: Click on the ‘Apply custom filter’ button.
Step 2: Enter the word or sentence to return files that contain them. Select the user’s account you want to search through you can leave this field blank to search your entire domain’s Drive or enter a user, Google Group, or Org Unit to search through them only.
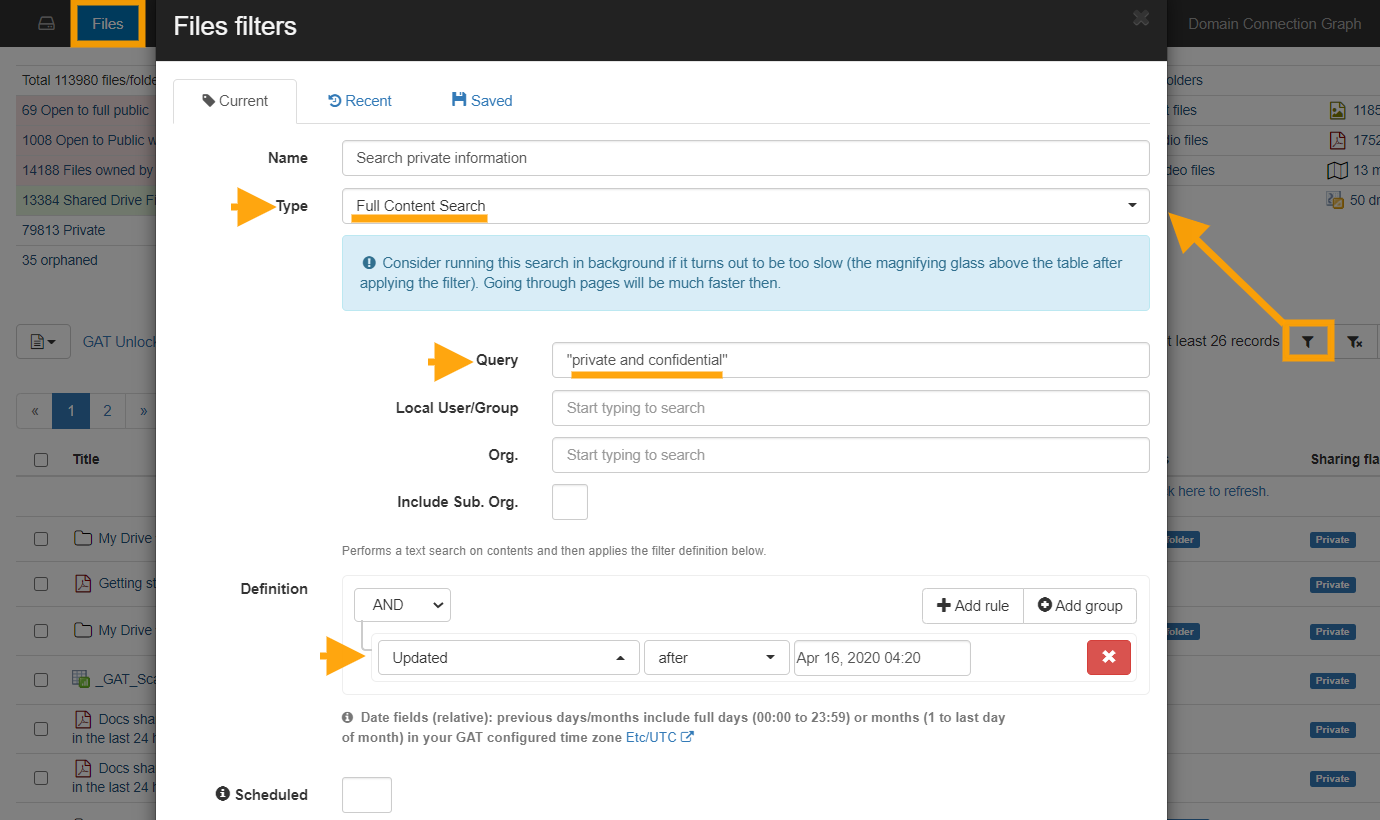
You can also use multiple rules in the Definition section of the (Query builder) Apply custom filter. I used the Updated search parameter. Once you click on the Apply button the search will begin.
It might take some time depending on how many files you have across your domain.
Step 3: Select the files you are interested in, remember that these files contain the sentence “private and confidential”.
Click on the ‘Files operation’ button and then select ‘Create new access request’.

Step 4: Next we will select a date in the future, we will have access to these files until this date. You have an option to write to your security officer explaining why you need access to these files.

Send the request to the Security Officer(s) for approval.
The following email will be sent to the Security Officer.

The Security Officer can click on the link in the email and will be taken to the approval area (Access Permissions) in GAT+.
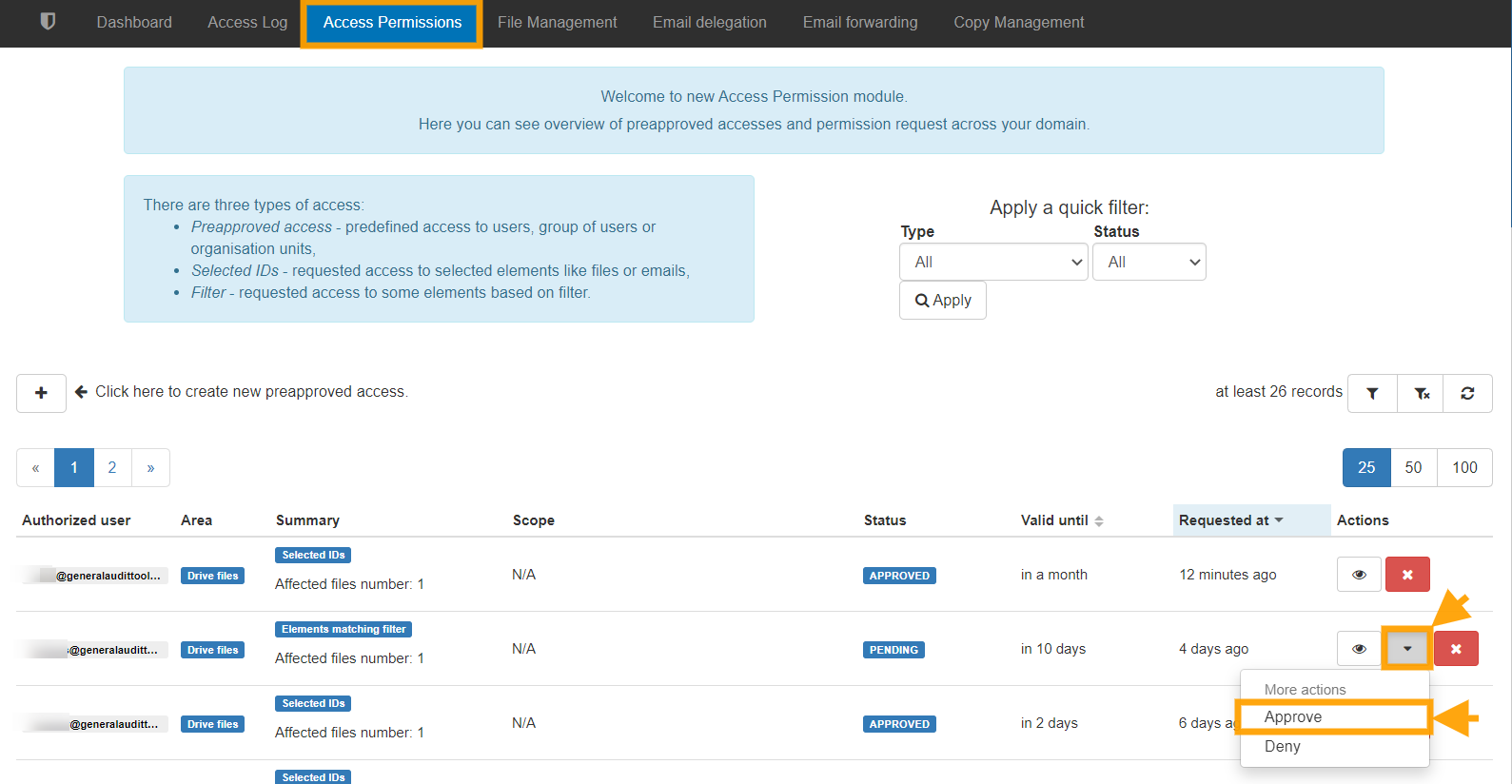
When the Security Officer approves access an email will be sent to the requesting Administrator/delegated auditor informing them. The Admin then opens the ‘Access Permissions list’ menu again and can see the full list of their Access requests along with the time left for each request to remain valid.

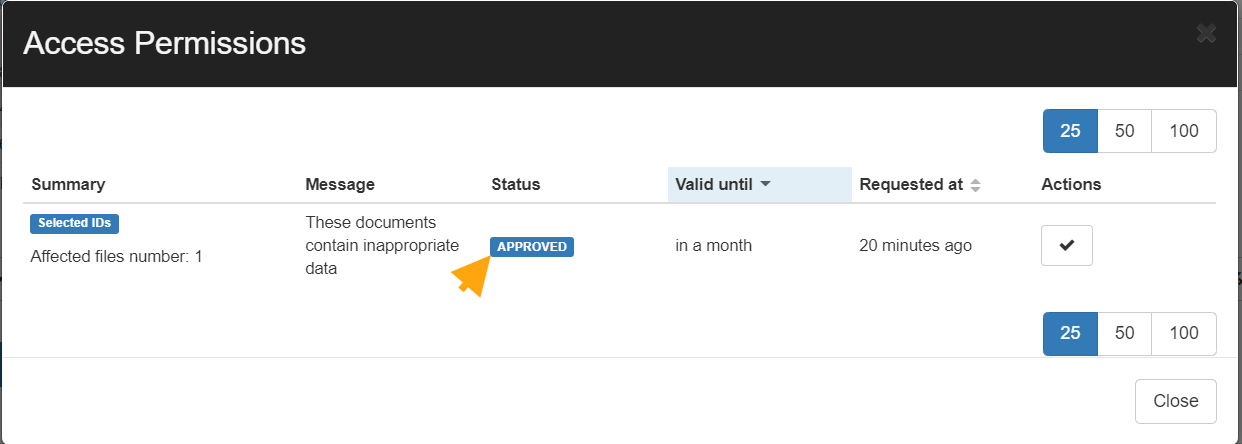
Once the request is selected a new window will open with the results, on the right-hand side those files will have a new tab called ‘Actions‘ under that the requestor can Download or Show file the contents silently without the owners’ awareness.

Pre-approved Access for Admins to All Files for a Range of Users
If your Super admins wish not to get Security Officer approval every time they want to make file permission changes or to view file contents, a security officer can give them pre-approval.
In the Security Officer section on the GAT+ sidebar menu, select ‘Preapproved Access’ and then click on the ‘+’ button to add a new Preapproved admin.
Once clicked a new ‘pop-up’ screen will appear.
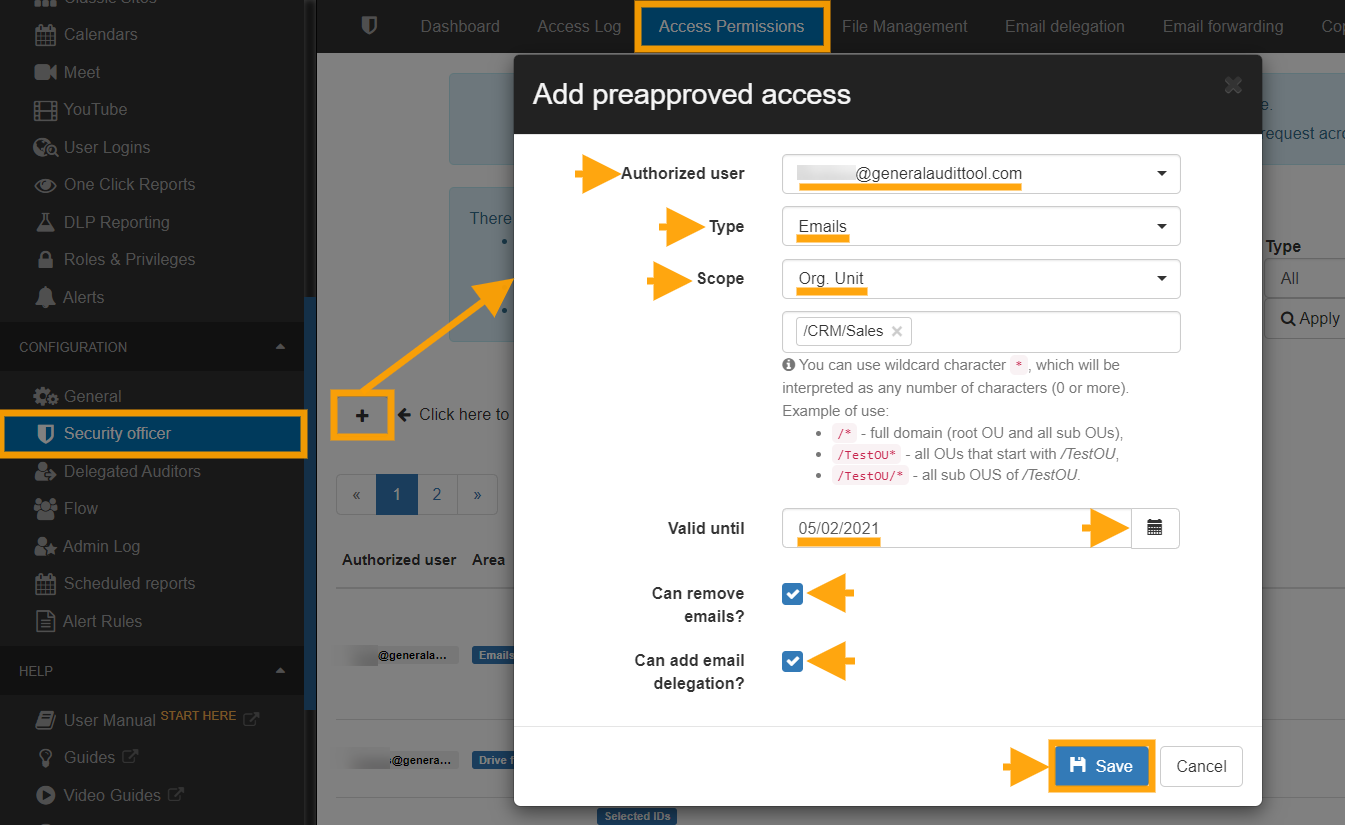
Here the security officer can add the email address of the Super Admin, the OU over which they will have access, they can select a full OU tree and set approval access until a certain future date. In the above screenshot, I gave Alex (super admin) access to the Support OU
Multiple different approvals can be given by the security officer, including several to the same Super Admin, each covering different scopes.
Changing Ownership of an Entire Folder Tree
Another feature of ‘Unlock’ is that it enables an often requested task of moving an entire folder tree, root folder and sub-folders, from one or many owners to a new owner.
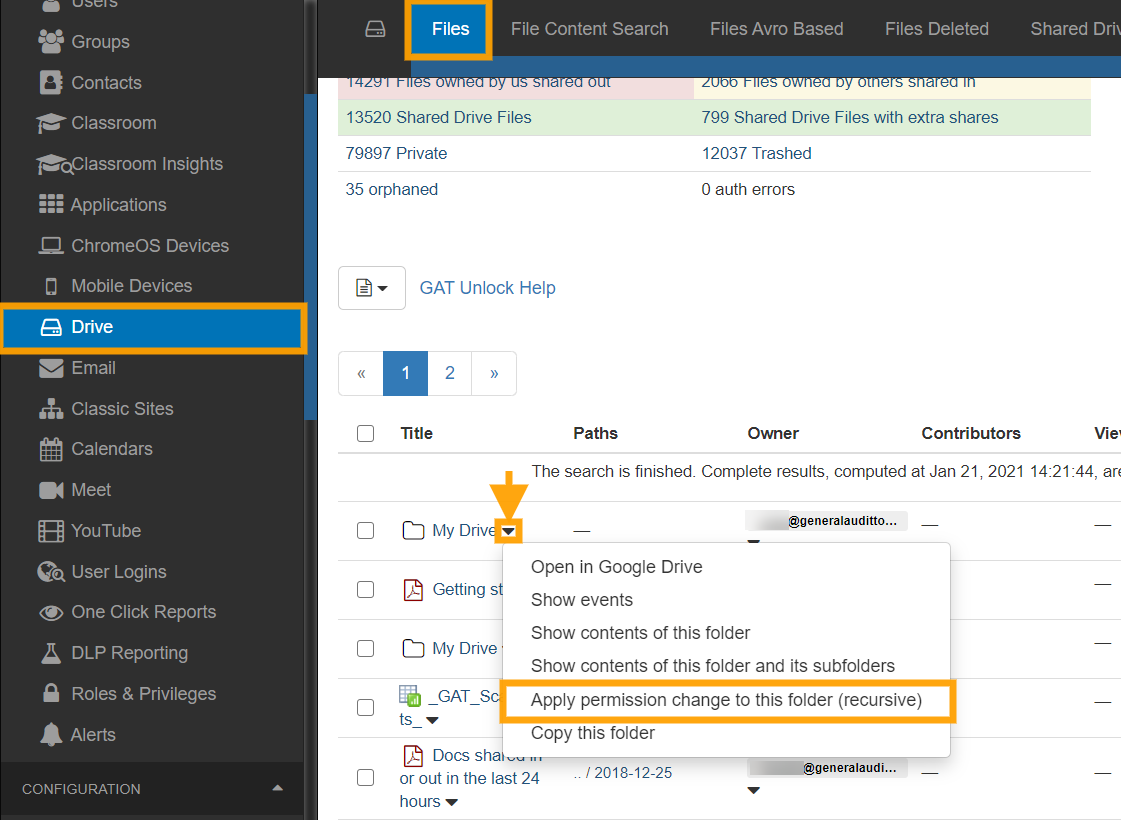
This task is completed with the File Management tab. Use the drop-down menu button next to the folder name to see the options. Click on Apply permission change to this folder (recursive). When the File Management option menu appears, enter the new owner’s email address. And make sure to remove the previous owner as editor.
Note: When changing ownership, the previous owner is added automatically as an editor. You can “deny access for the old owner” if you choose that option.

This is an ideal feature for consolidating a shared folder structure, or handling leaving staff or students.
Delegating Access to an email account
GAT+ allows Admins to delegate access for a User account to another User for a certain period of hours. This may be for business purposes but it also facilitates the fast search and viewing of all the account emails via another user’s browser.
BEFORE USING: Please ensure email delegation is allowed for users in your domain. Go to the Google Workspace Admin Console and under Apps > Google Workspace Apps > Settings for Gmail > User settings check if the email delegation box is allowed for your domain.

Launch the GAT+ tool, enter the User Audit section and click on the Email Info Tab.
In the Email Info Tab, select any user and click on the Actions button to add an email delegate to their account.
You have the ability to remove existing mail delegation which is already in place as well.

Here the Admin can select the account they wish to gain access to, then select the account they want to give this access to and finally select the number of hours they would like delegated access to be approved for. Once the request is sent, the Security Officer will still have to approve before the delegation is created.
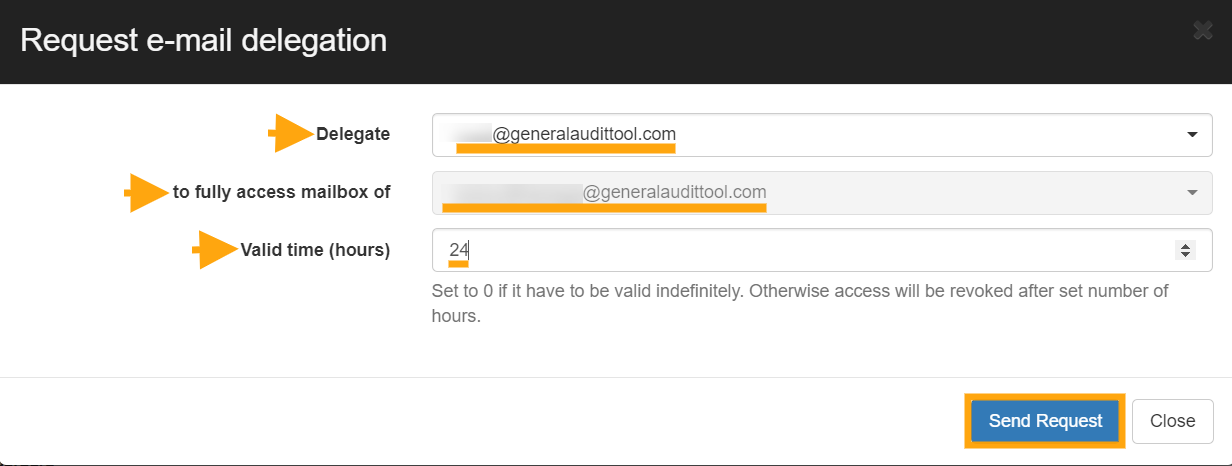
Once approved the delegated account appears in the accounts drop-down list when the profile picture is selected in Gmail.

The delegation will automatically be revoked after the requested time period.
Note: If during the period of delegation, the account under audit, logs into their Google account and goes to their email settings, then under ‘Accounts’ the account owner will see that the Admin has granted delegated access to the account.
In addition, if the delegated user reads any unopened email in the audited account, this email will be marked as ‘read’.
Delete Spam, Inappropriate or Accidental Emails
There are multiple reasons to have the ability to identify and remove emails that have been received by all or any of your domain users. Here are some unwanted scenarios:
- An email is sent to the wrong user or group
- An email contains inappropriate content
- An email that contains sensitive information
- An email that has gone past spam filtering or is a phishing email.
GAT+ allows Admins to delete these emails from all accounts at once.

We recommend using ‘Email Content Search’ for tracking down these emails. It is a ‘real-time’ search that is highly configurable (see ‘search tips’ link beside the search box). In the screenshot above we use the example search parameters
“SEO proposal” in:anywhere newer_than:90d
This tells GAT+ to search in all emails, for all users and look for emails that contain the words “SEO proposal” which are also newer than 90 days. When the results come back to select the emails you wish to view/download/delete then click the “Email operations” button and select “Access permissions list”.
When you search if the result cannot be displayed in a timely manner, the search goes into Background search.
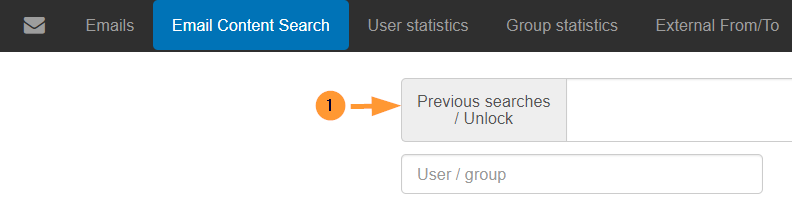
You can access those searches by selecting ‘Previous searches‘.
All older or background searches will be displayed there.
Once completed, under the ‘Actions’ tab select the green checkmark to display the results.
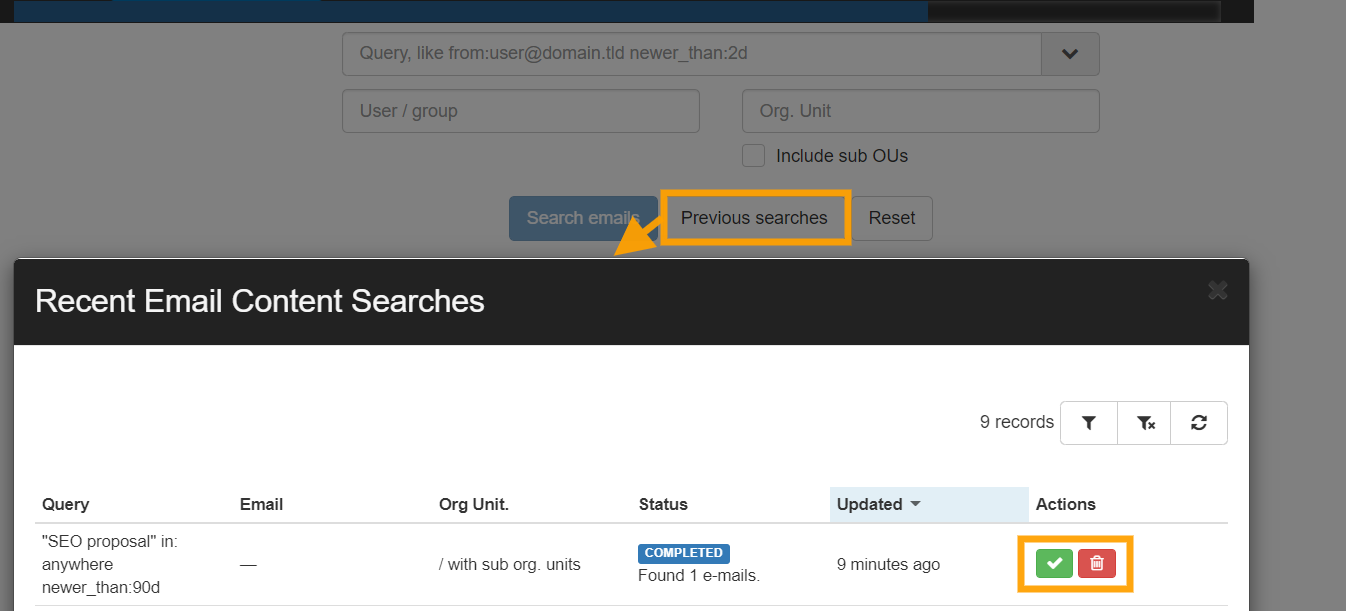
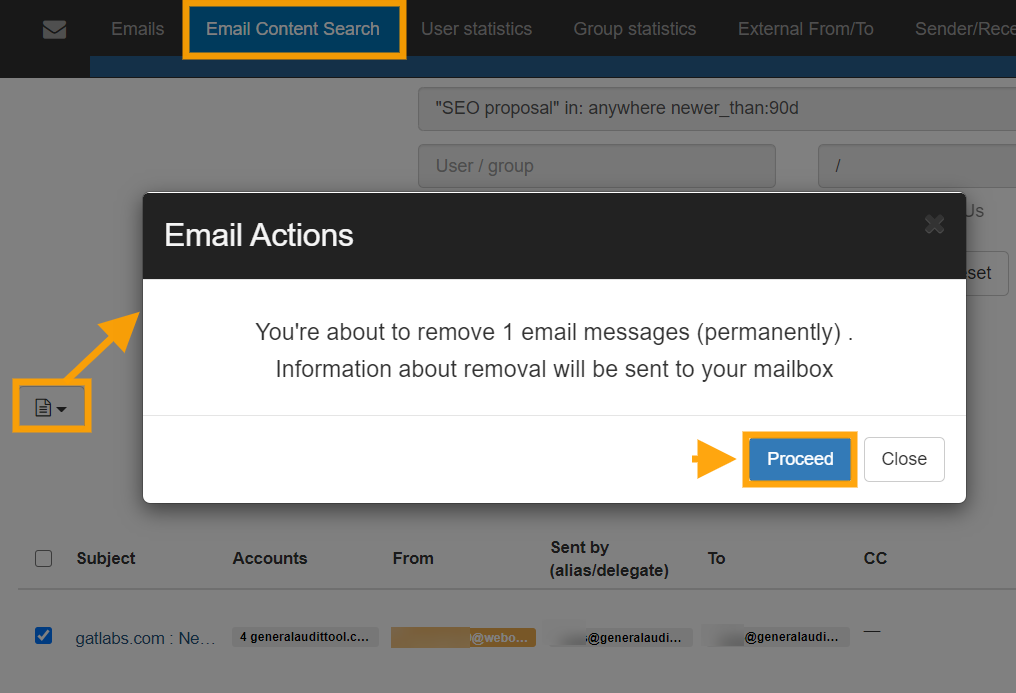
Once the emails are selected, click on the ‘Access permissions list’ button and send a request to your SO (security officer). Your SO will have to approve your request.
Before sending the request if you intend to delete the emails rather than just view or download them then check the ‘Allow removing emails’ box.

As an option, you can send a message to the Security officer giving a reason for the investigation.
After performing those steps please select and click ‘send request’ and wait for approval to be returned from the Security Officer.
You can check all the requests to the SO in the “Security officer” section in GAT+.
Note: You can not self-approve your own request. An admin sends the request the Security officer approves.

Once your request has been approved, you will receive an email notification stating that.
Note: While you wait for the approval, you might use the tool for other searches. When you come back to “Email Content search” click on the Previous searches/Unlock button.
You can then delete one or all of the emails using the drop-down option in the Emails Operation button.
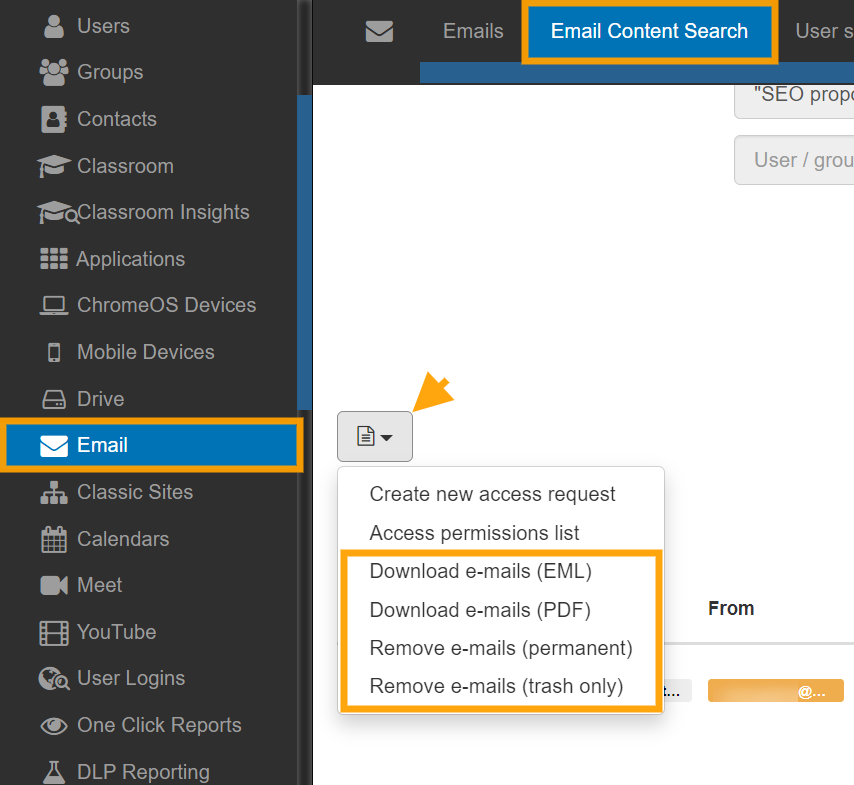
By default, you can send the emails to the user’s Trash folder on their Gmail but if you wish to permanently delete these emails then select ‘Delete permanently.
Pre-approved Access for Super Admins to all Emails
To enable pre-approval for Super Admins navigate to the Configuration section of GAT+ and enter the security officer area.
Once there click on the Preapproved Access Tab and click on the plus icon “Add new pre-approved access”.
Your security officer will have to select you (super admin) to have pre-approval over users across your domain.

This is ideal for situations where Admins do not need to get constant approval to view/download or remove emails.
An example would be in an education domain where the Super Admin would have full open access (view/download or remove emails) for all Student OU’s but would still have to get selective approval from the security officer to access an in the Staff or HR OU.
For a single OU, level adds value like /Staff (Note, this will not grant access to the OU /Staff/IT unless “Sub Org. Units equals Yes!).
In the above screenshot, I put Ferdows (Super Admin) to have pre-approved access to the entire domain by selecting / for the Org Unit and I made sure to cover all Sub-Org Units. / means the root User Org. Unit.
They have access to remove and add email delegations as well because I enabled the last two option which is “Can remove?” and “Can add email delegation”.
Non-Super Admin Auditors
This feature is ideal where Super Admins want to delegate the audit function to local managers or regional security personnel.
GAT+ allows the Admin to select the scope of users that will be covered by the Auditor.
The admin can also select what audit areas to be included.
Auditors will have access to Audit areas and for the scope, they are given only.

What is a Security Officer?
See Details
The Security Officer is a user from your domain that is responsible for approving or denying the changes requested by any Admin.
What do I need to enable my Security Officers?
To enable Security Officers you would need to have a paid licence with the Admin Plan or higher for Enterprise and is included in all the plans for Education.
How can I configure my Security Officers?
To configure your Security Officers you would need to firstly have a paid licence as per the previous question and secondly email us at unlock@gatlabs.com
Only the GAT Labs team can add, remove or change the Security Officers in your domain.
For easier management, it is recommended to have at least two Security Officers in the domain. If you don’t have a second person you can create a service account such as unlock@yourdomain.com
Who can be a Security Officer?
The Security officer can be any user of the domain, it does not matter what Google Workspace privileges they have.
What products require a Security Officer approval?
GAT Unlock within GAT+ and GAT Flow
What type of actions require a Security Officer?
- Allow setting up Email delegation within GAT+
- Allow setting Email auto-forwarding within GAT+
- Allow change of ownership of Drive files within GAT+
- Allow altering Drive files by adding and replacing existing permissions
- Allow copying Drive files
- Allow viewing File content
- Allow download of the File content
- Allow viewing Email content
- Allow download of Email content
- Allow Admins to onboard offboard and modify users within Flow
How does the Security Officer workflow approval works in GAT+?
When the Admin sends a request for any action that requires Security officer approval, an email will be sent to the officer.
The email will look similar to the screenshot below, depending on what is the request for.

Clicking on the link ‘click here’ will lead to the Security officer tab in GAT+.

By default selecting the link from the email will lead to the exact field from where the request can be approved or denied.
In each of the section, the Security officer just selects the request and approve or deny it.

File management will have the file permission changes required, Folder copy for copying folders, Grants is for view or downloading of files and emails. More information can be checked in the Dashboard section.
How does the Security Officer workflow approval works in GAT Flow?
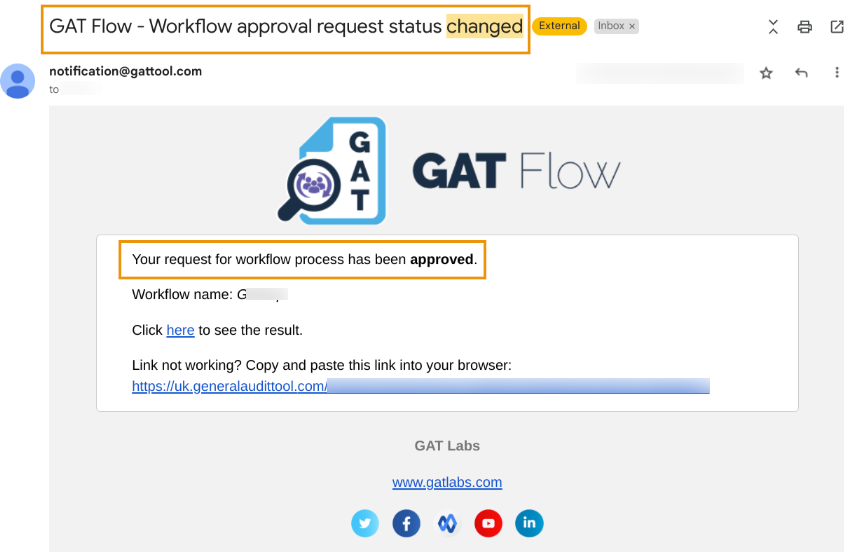
When the Admin creates a workflow and sends it to the Security Officer for verification, an email will be sent to the officer.
The Security Officer will receive an email notification that the workflow is waiting for verification.

By default selecting the link from the email will lead to the exact field from where the request can be reviewed and then approved or denied.

During the approval process, a message will appear confirming that the approval is indeed intended.

Once approved, the workflow is scheduled to run.
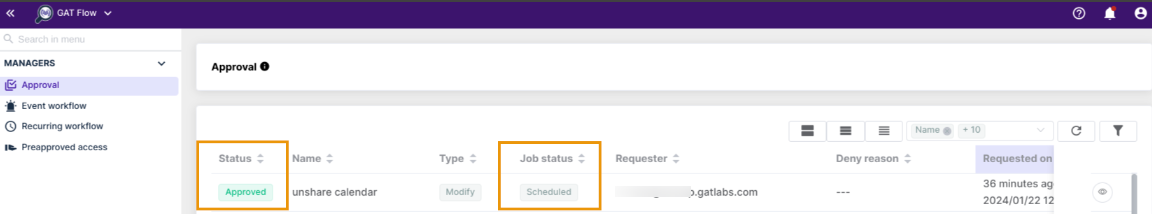
The workflow Requester receives an email notification about the approval.
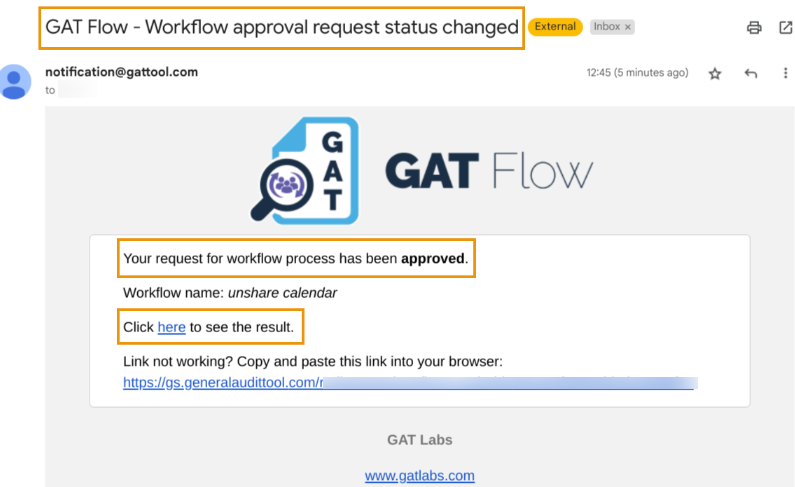
Once completed successfully, another email is sent to the Requester informing them about workflow completion.

By default selecting the link from the emails will lead the workflow Requester to the exact field of GAT Flow from where the results can be reviewed.

NOTE:
- Only the GAT Labs Staff can enable Security Officers. Please contact us at unlock@generalaudittool.com for more information.
- For easier management, it is recommended to have at least two Security Officers in the domain.
- GAT Unlock is not activated during trials for security reasons.
FAQ’s – Security Officers in GAT
See Details
What is a Security Officer in GAT?
Security Officers are users of the domain who can approve or deny any requests from any Admin or Delegated Auditor in GAT+ and GAT Flow.
A Security Officer does not necessarily need to be a Google Super Admin or a Delegated Auditor. They can also be a regular user in your domain.
How can I add a Security Officer?
To add a Security Officer you must have a paid licence that includes GAT Unlock and/or GAT Flow
Security Officers can be added, edited, and removed only by GAT+ staff.
For easier management, it is recommended to have at least two Security Officers in the domain.
Check out this document to better understand the enablement process.
Can I test GAT Unlock and/or GAT Flow?
Yes, you can run a trial on a test domain. Otherwise, you’d need a paid licence with a plan that includes these products.
Check out our pricing plans for Enterprise and Education.
Please contact sales@gatlabs.com for more information.
How can I check my Security Officers’ list?
In GAT+ you can check who are the users who are set up as Security Officers.
Navigate to GAT+ > Configuration > General > Domain info > Security officers

How can I update my Security Officers?
Security Officers can be added, edited, and removed only by GAT+ staff.
To make updates to the current list, an existing Security Officer in your domain or the Approver (Senior Manager) can contact us at unlock@generalaudittool.com. We’ll gladly take care of your request from there.
What happens if my Security Officers or Approver left the organisation?
Please contact us at unlock@generalaudittool.com. We’ll need to run the approval process again then.
Check out this document to better understand the enablement process.

Add Users to an OU Depending on Their Department with GAT Flow
See Details
GAT Flow is a user management tool. It allows Google Workspace Admins to set conditional workflows for the nesting of actions that will execute when a certain specified condition is met. This paves way for complex workflows that might consider multiple conditions and actions. For such use cases, there is the option to align overlapping actions to tidy up the visual complexity explained in the example below. Let’s see how to set a workflow to add users to an OU depending on their department.
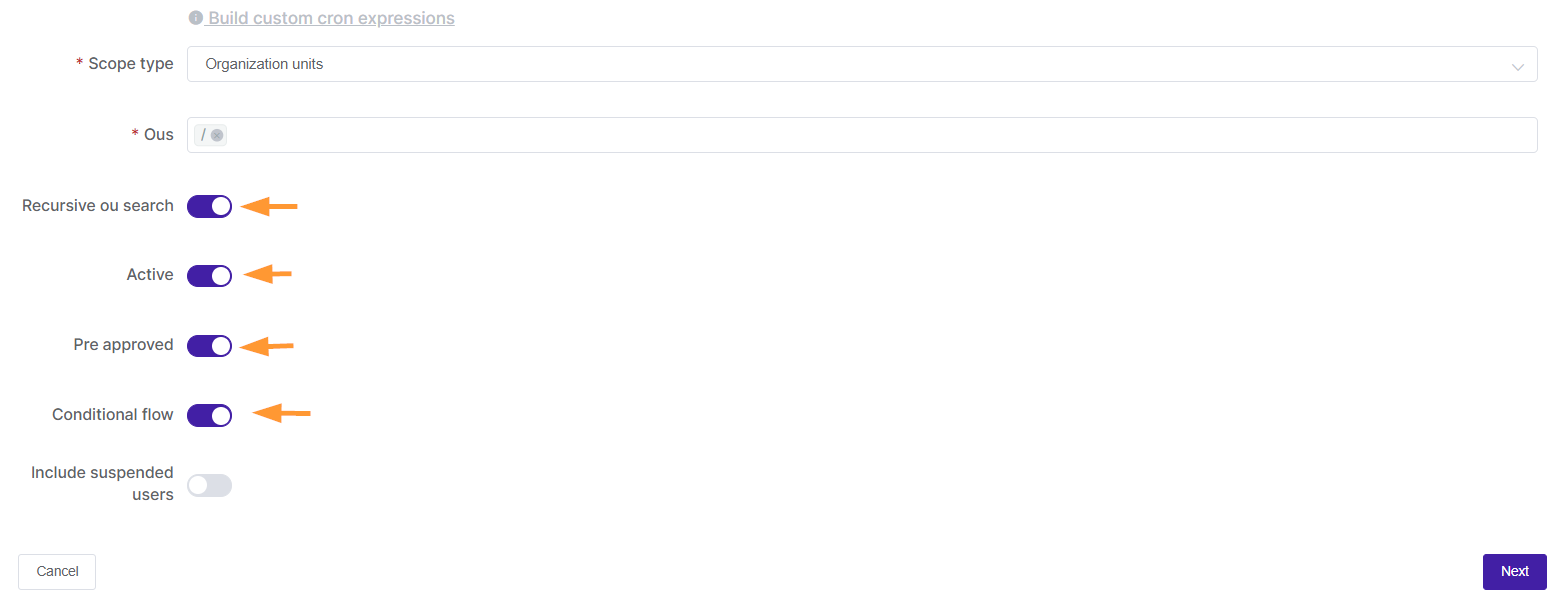
Step 1.
To add users to an OU, it’s best to set a recurring workflow that will run according to the time set by the workflow creator. Every time the workflow runs it will check the department conditions specified and run the following actions.

Step 2.
For this example, we enable the following options:
- Recursive OU search – capturing all sub-OUs of selected OU.
- Active – enable workflow.
- Preapproved – select to avoid needing the Security Officer’s approval after every time the report runs. A security officer has to only approve initially when this is selected.
- Conditional Flow – This will enable the conditional functionality in the actions menu.
Step 3.
Clicking Next will take you to the Choose Actions subtab.

Here you can add a Department condition.

Add action in case the condition is true. For this example, we are adding the action Change organization unit to the /Sales OU.

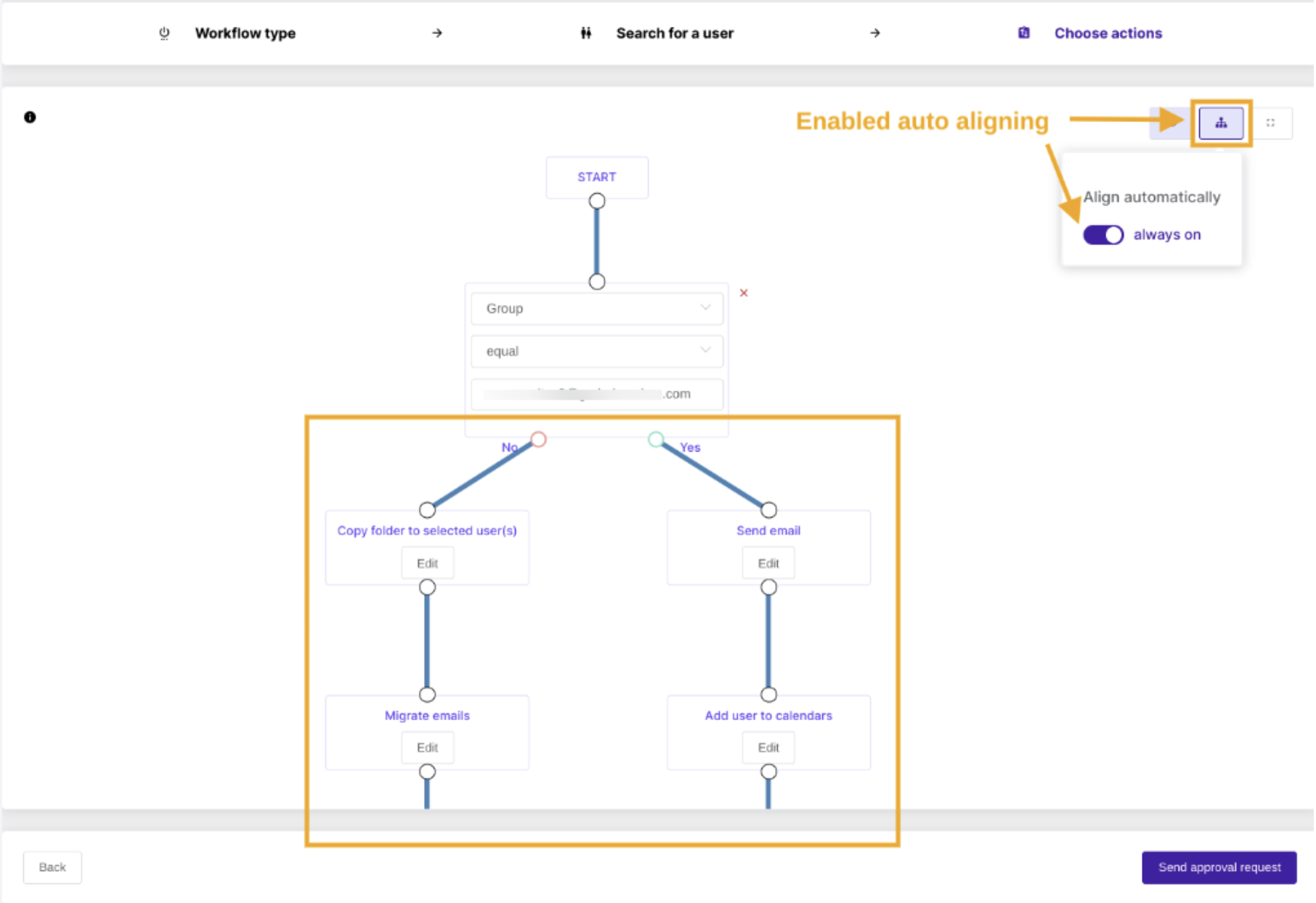
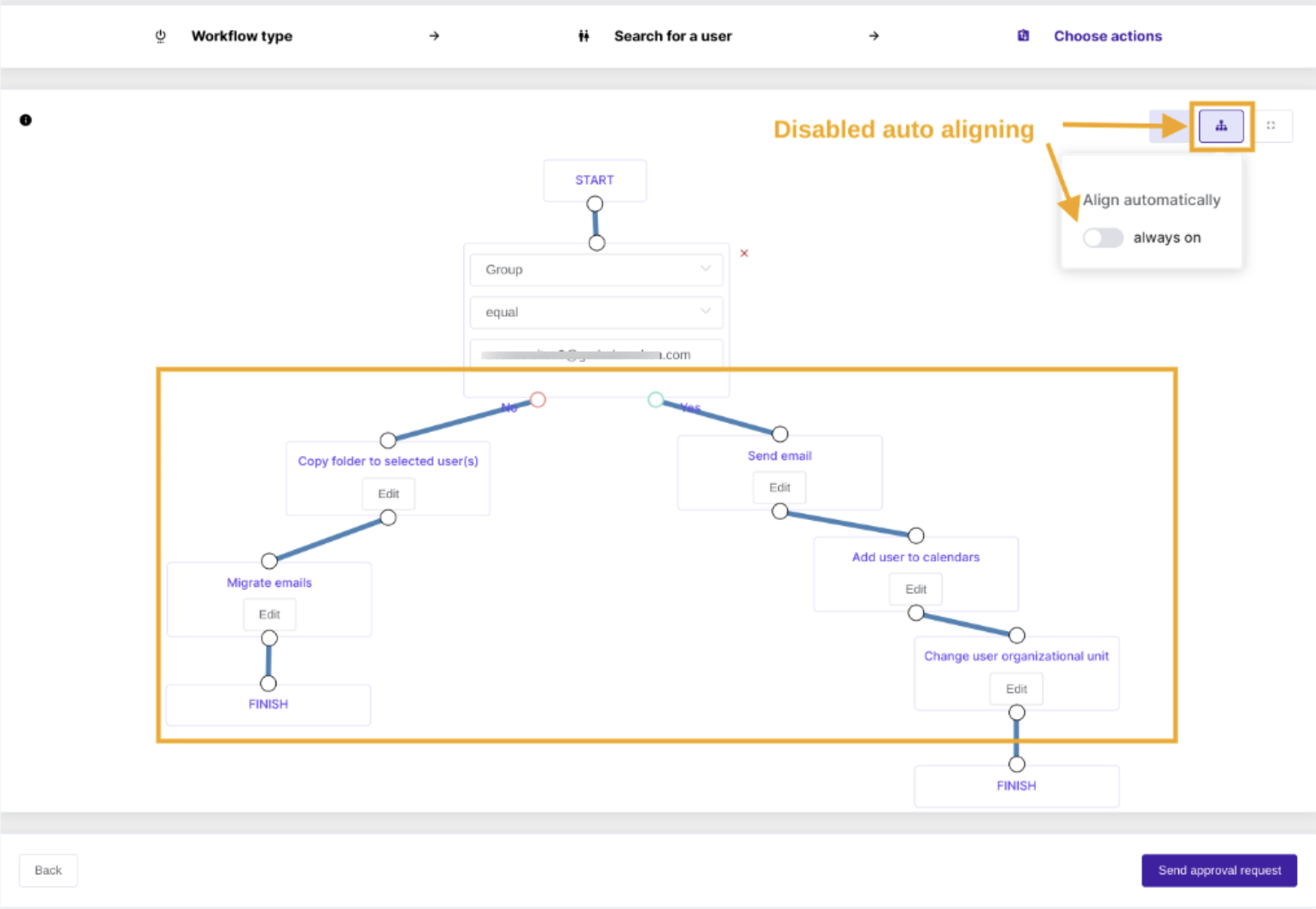
Repeat the steps until all the departments and relevant OU’s are captured in the Workflow. There may be many actions and conditions added, notice the align overlapping actions icon at the top right, this can be toggled and will align the view.
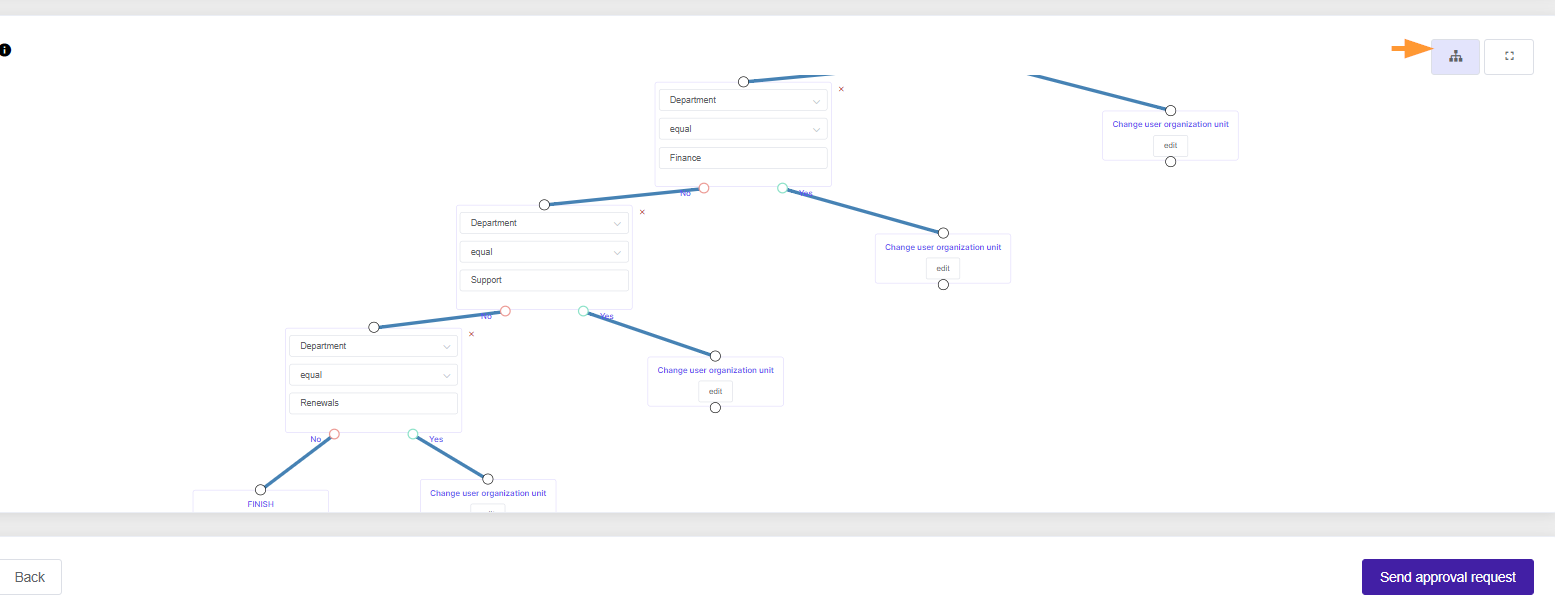
Remember to end the line graph for each node and then send the approval request.
Results
Once the workflow is approved, it will execute at the set time. To check the actions executed, toggle the results button next to the workflow.

The tool will navigate you to the workflow Results in the Workflow module. Select the eye icon next to the workflow to see in detail exactly the actions and users affected.

Selecting the figures will show in further detail the status of the actions executed for each user.


Related Posts
GAT Flow Settings Configuration
See Details
The GAT Flow Configuration section is available only for domain Administrators of Google Workspace and helps configure the tool to be as user-friendly as possible.
A domain Administrator can set up several options according to each domain’s needs under Configuration > Settings > Workflow.

Workflow Settings
You can configure the following available GAT Flow settings accordingly under the Workflow tab:
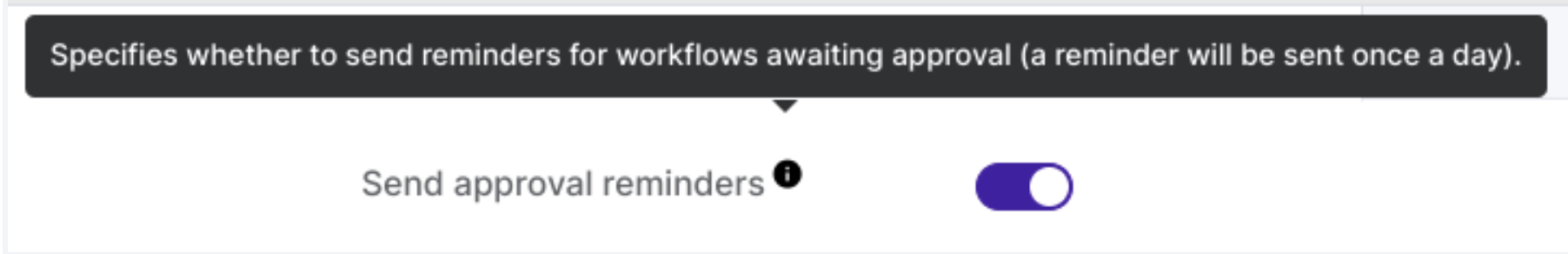
Send approval reminder
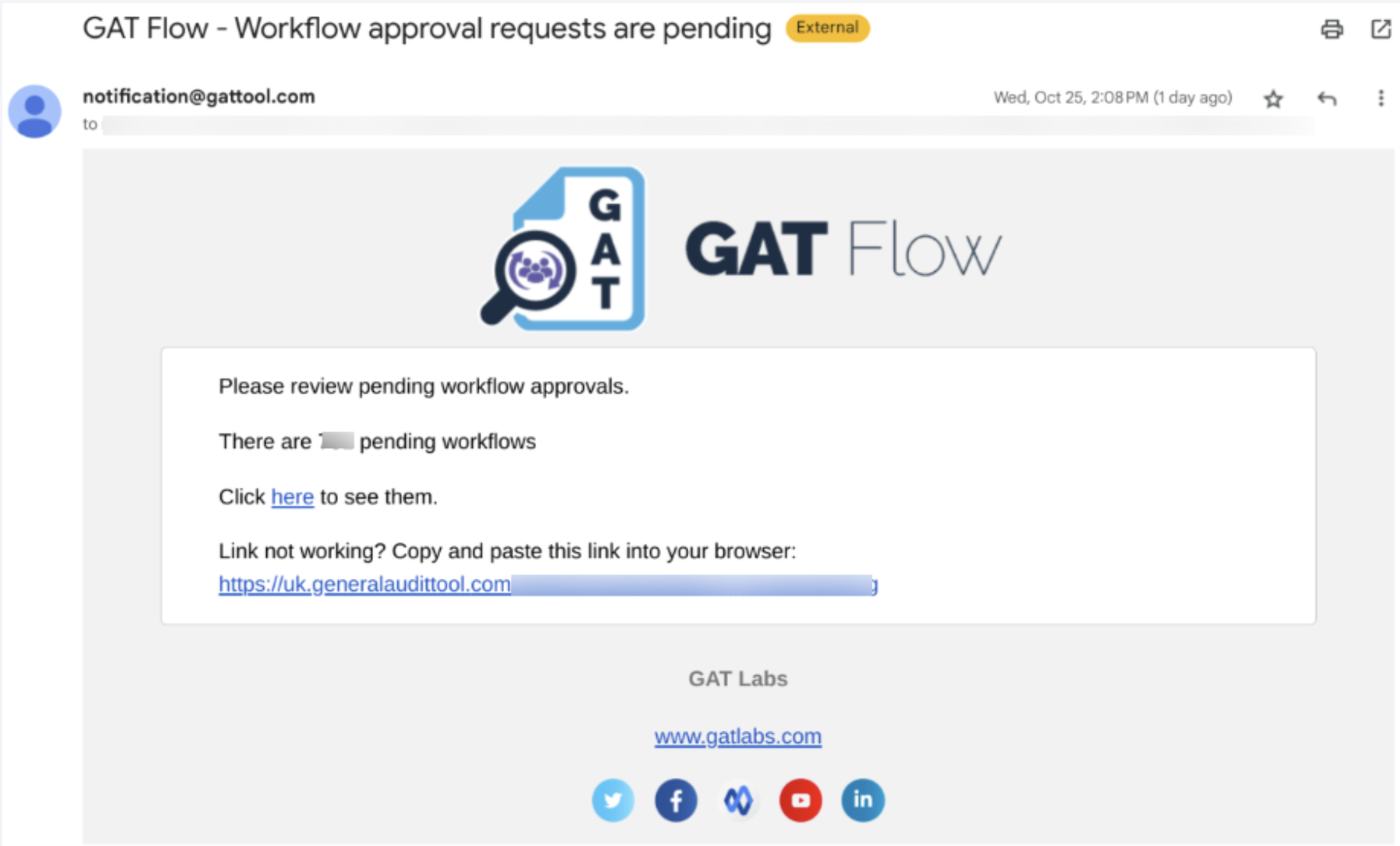
- Send approval reminder – this option allows an Admin to decide whether the reminder email for the workflows awaiting approval needs to be sent to all of the Security Officers, a reminder will be sent once a day if enabled
An email notification that each of the Security Officers will receive:
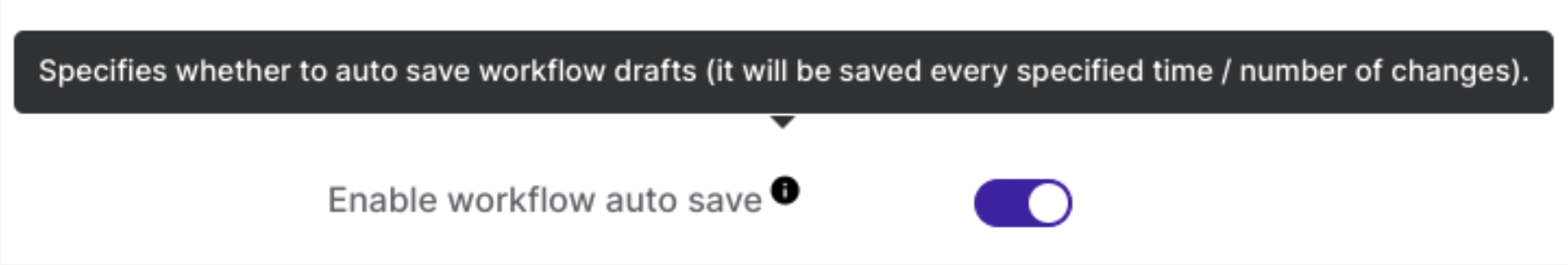
Enable workflow auto-save
- Enable workflow auto-save – an Admin can decide whether workflows should be automatically saved during the creation process to avoid losing them when the page is refreshed (useful for complex/advanced workflows that require longer preparation time)
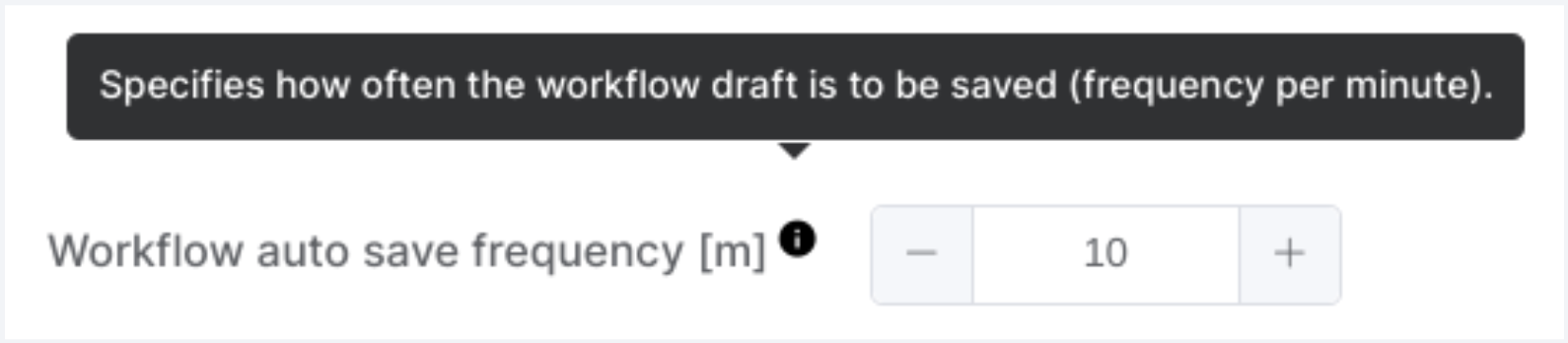
Workflow auto-save frequency
- Workflow auto-save frequency – set the workflow auto-save frequency in minutes to automatically save the workflow after that time elapses.
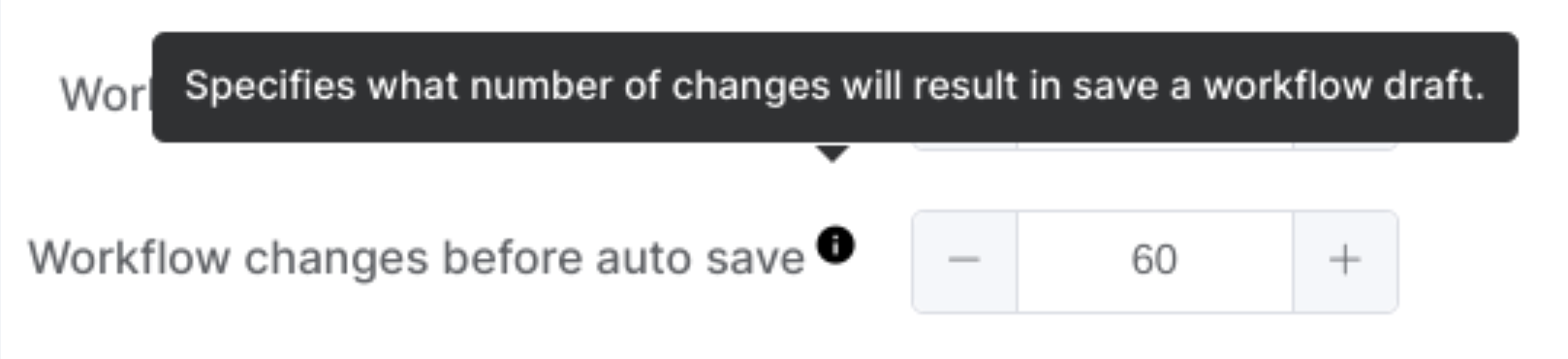
Workflow changes before auto-save
- Workflow changes before auto-save – Set the number of changes to the workflow that will trigger an automatic save.
Enable advanced workflow auto alignment by default
- Enable advance workflow auto alignment by default – an Admin can decide whether to enable by default auto aligning of the nodes in the conditional/advanced workflow
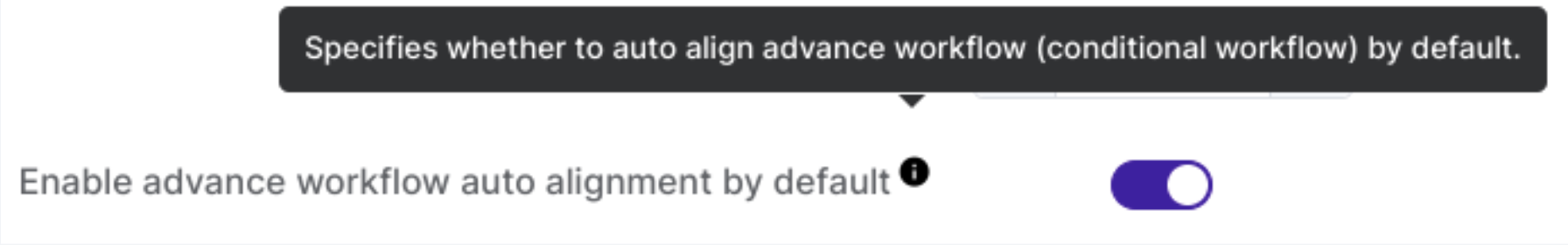
When you turn on auto-alignment, the system places all nodes in their default position.
When you turn off auto-alignment, you can arrange all nodes according to the workflow creator’s needs.
Enable advanced workflow node preview by default
- Enable advanced workflow node preview by default – an Admin can decide whether the node preview of the conditional/advanced workflow will be available
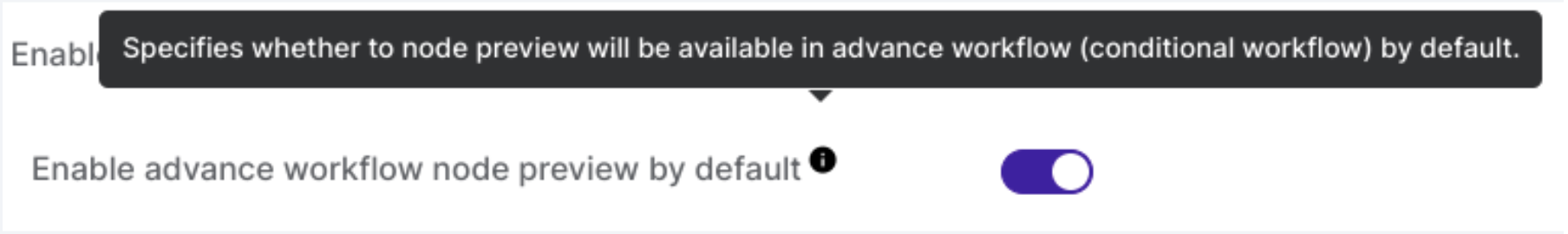
By default, enabling this option allows you to preview each node in the conditional workflow by hovering over its ‘Edit’ button.
Send notification about “Done” workflow to
- Define the person who will receive the email notification once the workflow is finished successfully; the workflow requester receives it by default


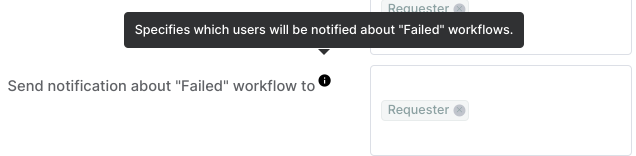
Send notification about “Failed” workflow to
- Define the person who will receive the email notification once the workflow is finished unsuccessfully; the workflow requester receives it by default

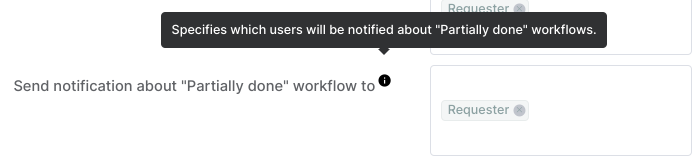
Send notification about “Partially done” workflow to
- Define the person who will receive the email notification once the workflow is partially done; the workflow requester receives it by default

Send approval status change notification to
- Define the person who will receive the email notification once the workflow approval status is changed; the workflow requester receives it by default

Workflow Tags
An Admin can create custom Workflow tags that help with identifying and sorting out workflows.
The default tags are as follows:
- Workflow – generated automatically by the system for the regular workflow
- Event – generated automatically by the system for Event-triggered workflow
- Recurring – generated automatically by the system for Recurring workflow
On top of the above default tags, an Admin can create a tag of their choice to be able to identify the workflows in a quick-for-them way (examples of custom tags are shown in the below screenshot).

Relevant posts
How to Create Workflow Tags in GAT Flow
See Details
Managing numerous workflows in your domain can be challenging. GAT Flow introduces a tagging system to simplify this process, allowing you to see what’s happening at a glance.
Creating Workflow Tags in GAT Flow
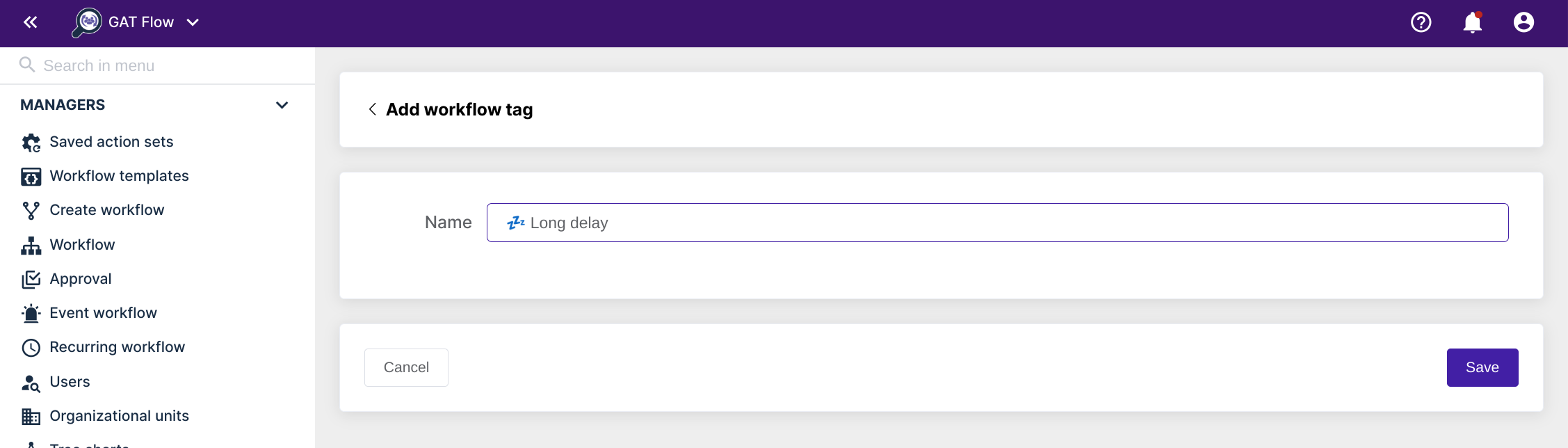
To create a tag, first go to the Settings section in GAT Flow.
Click the Workflow tags in the top right corner and Create tag.
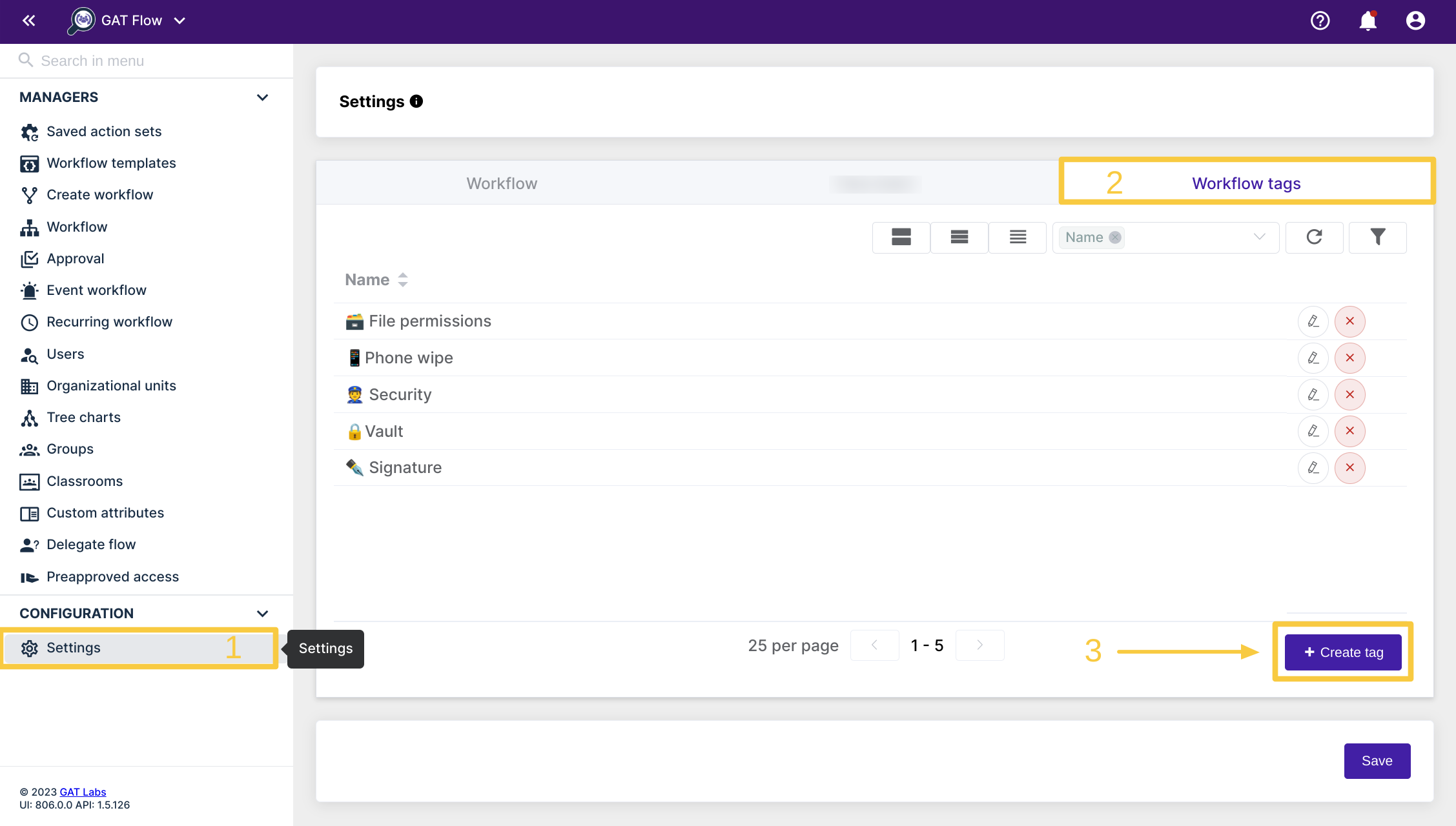
Enter a name for your tag and click Save.
That’s it! You have created your new tag and it is ready for immediate use.

Using your custom tag
You can apply your new tag to any new workflow you create. Just click on the ‘Workflow tags’ field when creating any workflow to see your available tags.
You can add multiple tags to a single workflow if you wish.

In the Workflow section, you will see all the previously run workflows, alongside the draft workflows. The column labeled workflow tabs will show you the tags that each workflow is given.

Each workflow receives one tag by default.
Standard manual workflows that were made from the ‘Create workflow’ section will be given the green label ‘Workflow’
If the workflow is an Event workflow, it receives a red ‘Event’ label.
Recurring workflows will receive a yellow label that reads ‘Recurring’.
Finding workflows from a specific tag
In the Workflow section, use the filter icon to select the applied tag, helping you quickly find previously tagged workflows.

Finally, click ‘Apply’ to display the results.


GAT Shield Configuration Instructions
See Details
GAT Shield Extension – How to Deploy
See Details
Deploying the GAT Shield Chrome Extension
In this document, we will cover the deployment steps of the GAT Shield extension.
To start navigate and login into the Google Admin console
In the Admin Console click on Devices
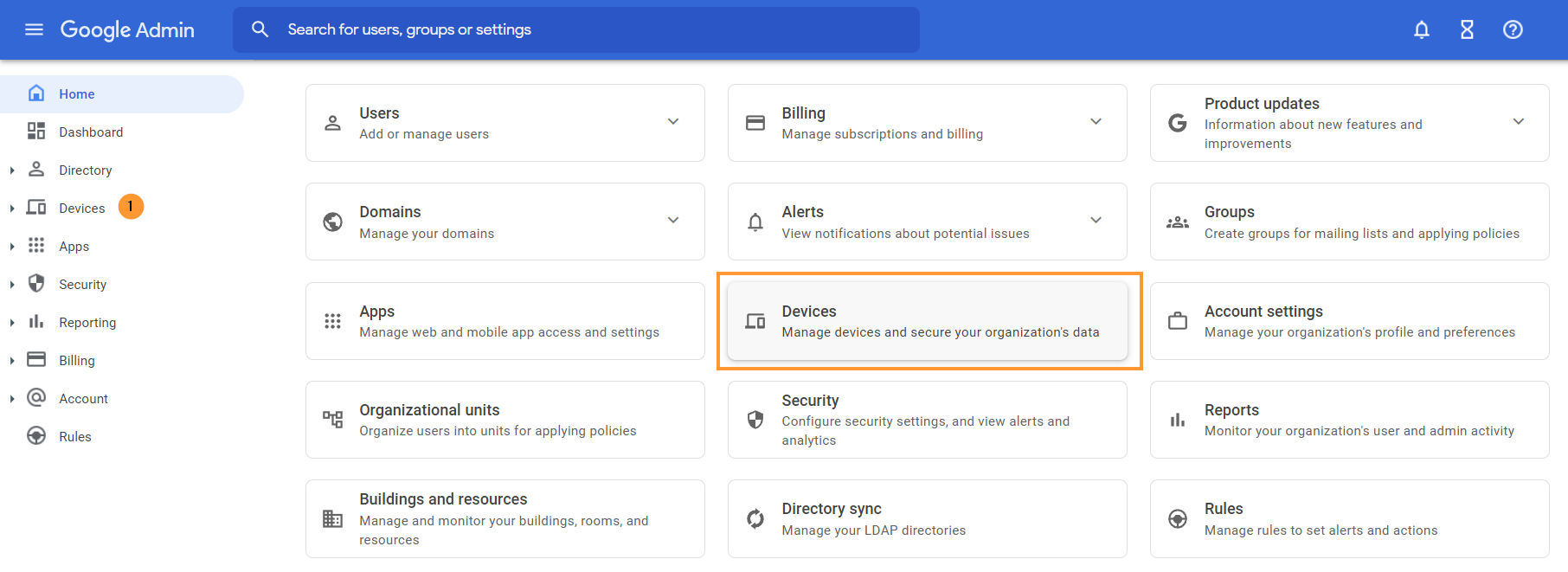
From the menu on the left navigate down to Devices >Chrome >Apps & extensions > click on Users & browsers
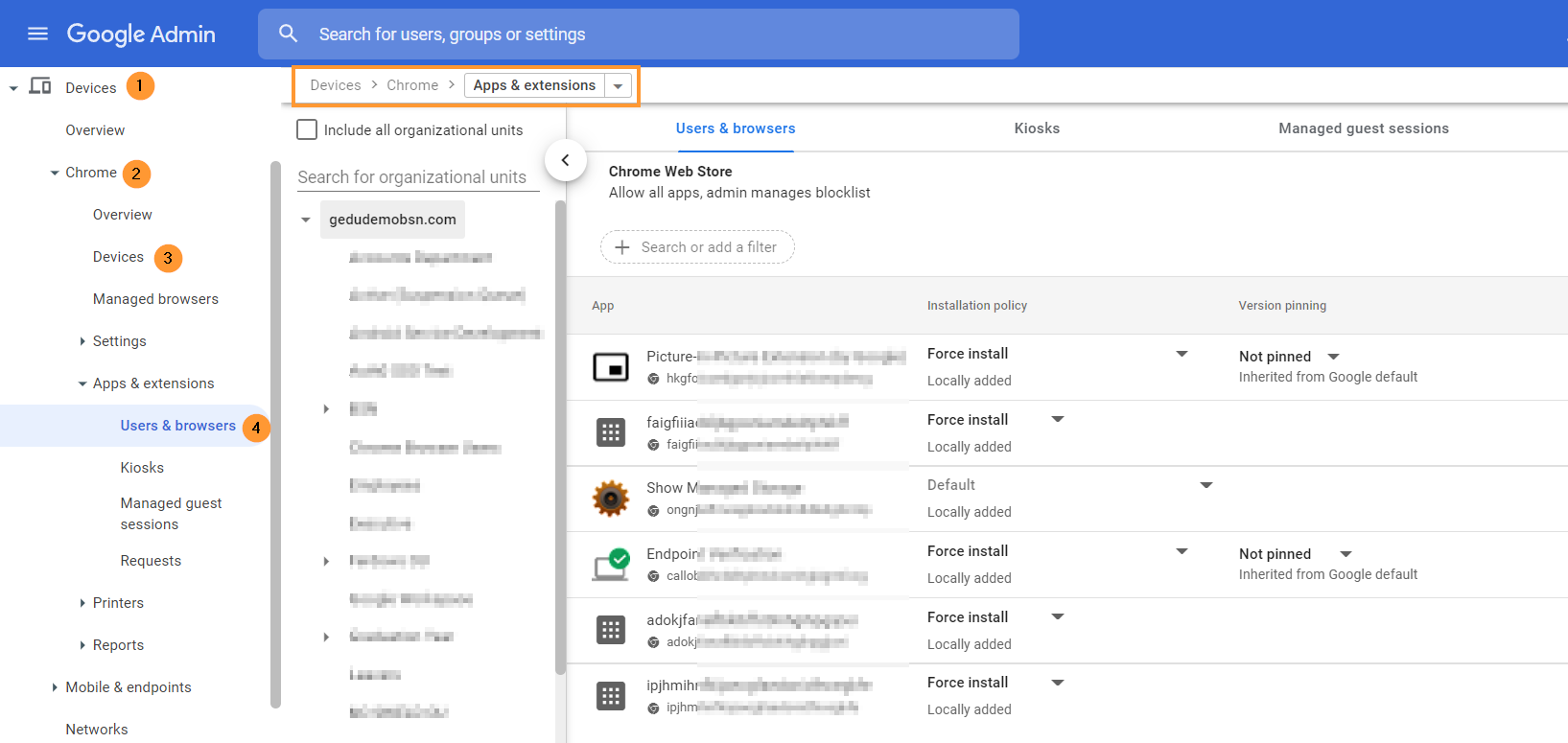
A new page will be displayed.
Install
To install the GAT Shield extension, choose the root Org Unit or a sub-OU where you want to deploy Shield into.
On the bottom right side, click on the Yellow + button
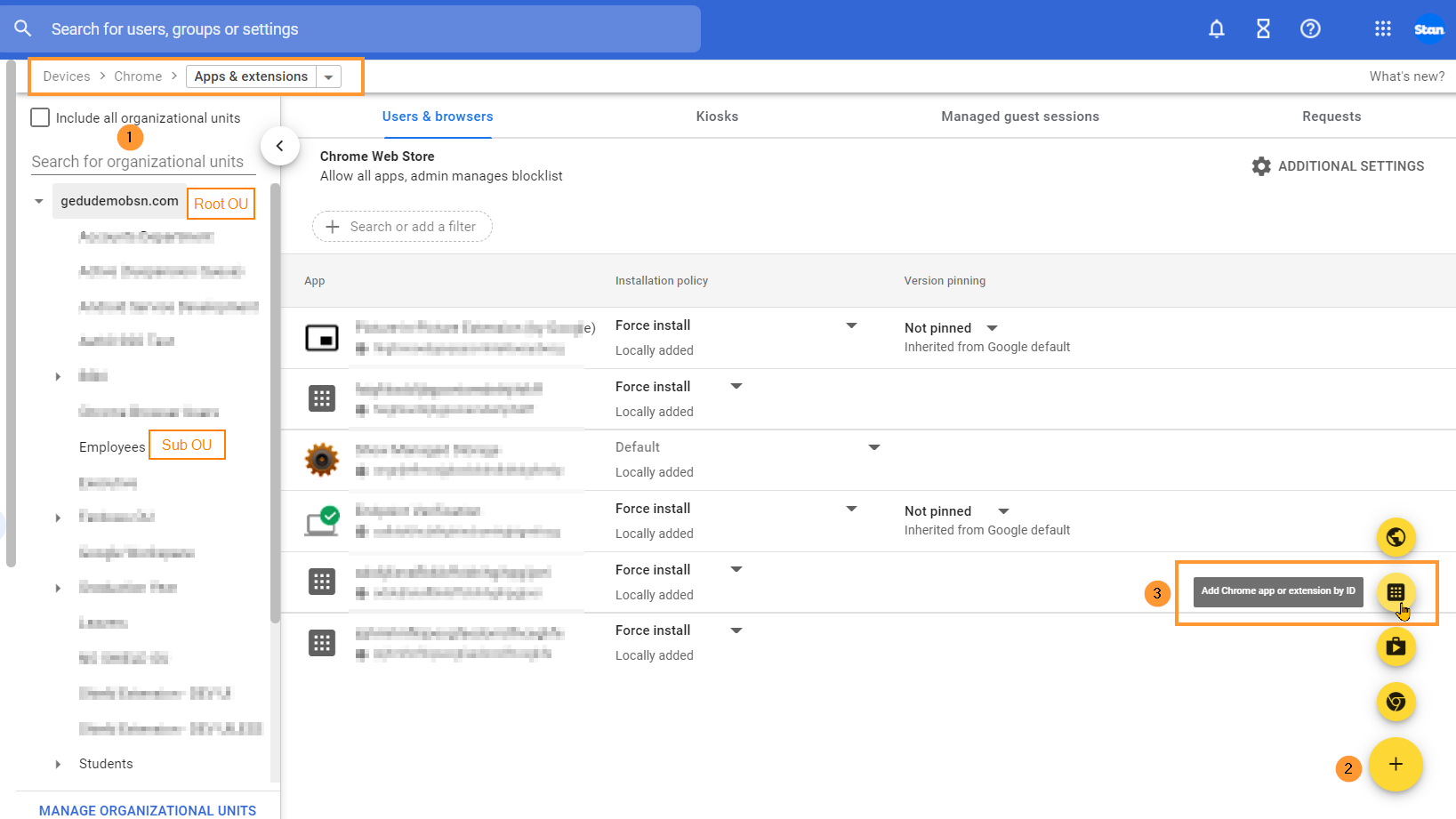
Select the Add the Chrome app or extension by ID option.
NOTE: A pop-up window will be displayed, select the From a custom URL option.
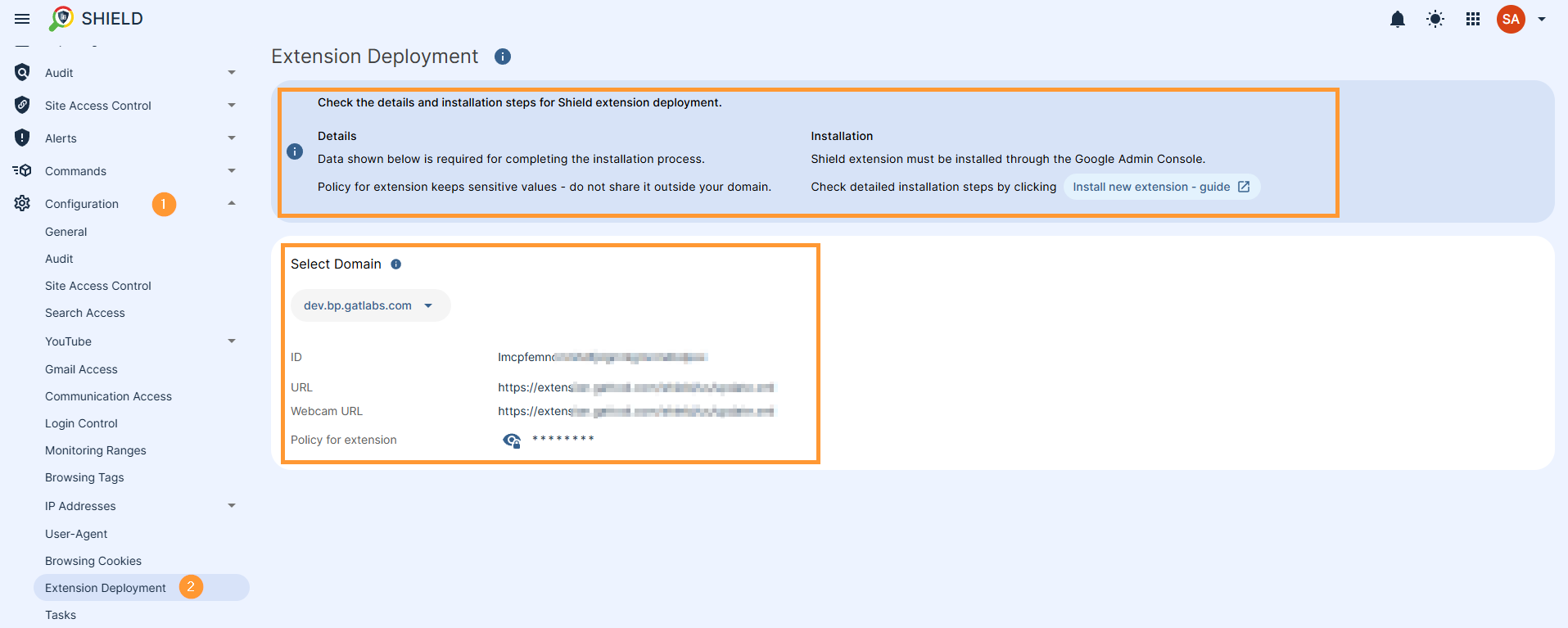
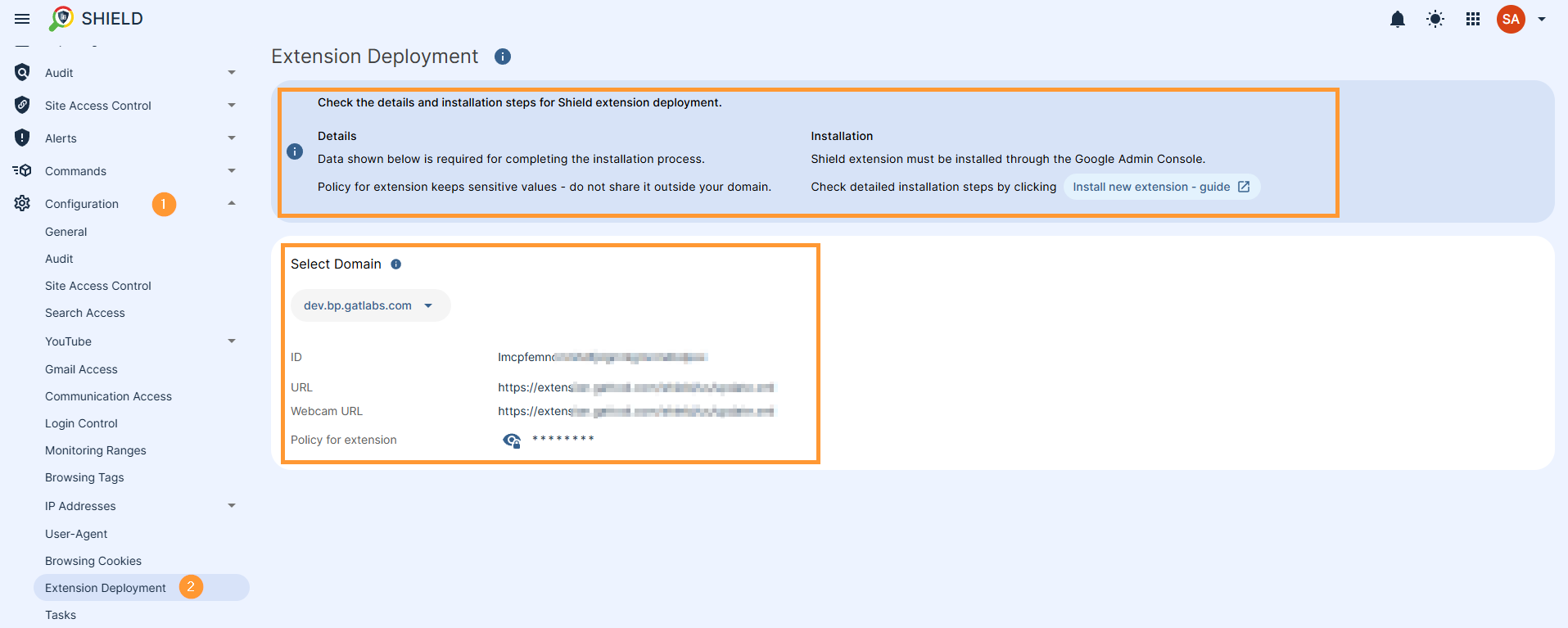
You’ll find both the ID and the URL required for this step in the GAT Shield application under the Extension deployment section.

Enter the Extension ID and URL of the extension.
To access and view the Extension ID and URL, navigate to GAT Shield > Configuration > Extension deployment.

Click Save.
The Shield Extension is now installed.
Click on the newly installed extension. You will see a pop-up window on the side. In the Installation policy, click and select Force install.

Scroll down on the same window to the bottom of the page to find the Policy for extensions.

Enter the Secret key – taken from GAT Shield under Configuration – Extensions deployment.
Under the Permissions and URL access field, click on and select Allow all permissions (2).

After doing all the changes, click the Save button on the top right.
Result
Shield will be installed for the users of the selected Org. Unit. It would depend on Google when the extension will appear on the end-user accounts.
Given that the users are logged in on Chrome browser with their Google Account, it should take a few minutes to be propagated to the end users.
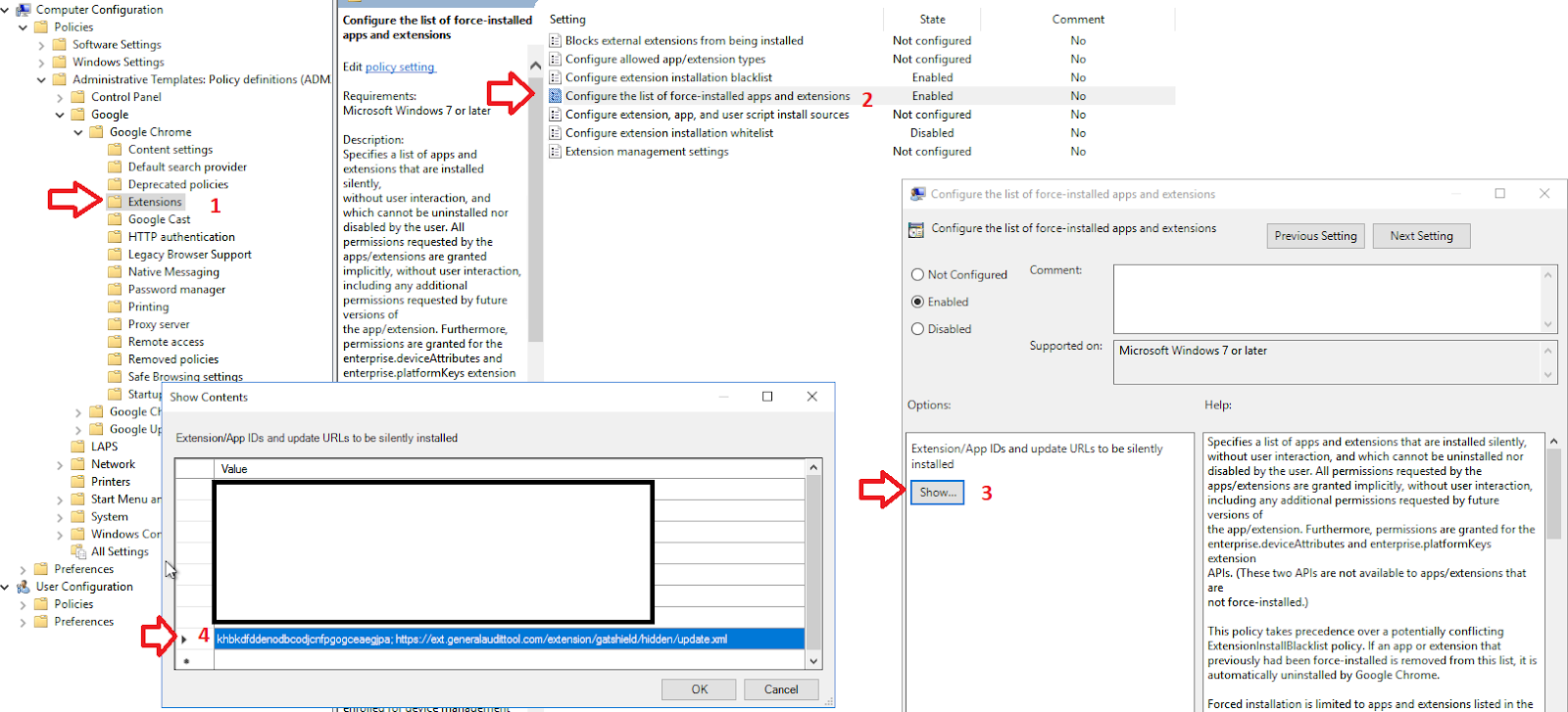
Deploying GAT Shield Extension using Microsoft Group Policy Objects (GPO)
First, apply the Chrome ADMX Group Policy using the steps found at this Google support article.
Navigate to Computer Configuration> Policies> Extension > Configure the list of force-installed apps and Extension
You are required to specify which Chrome extensions should be automatically installed (force-installed) for the users via Group Policy settings.
Next, you need to enter each extension ID and installation URL into the Group Policy setting.
You’ll find both the ID and the URL in the GAT Shield application under the Extension deployment section.

After you have configured the Chrome policy to force install the extension in Group Policy, you can assign this policy to particular groups of computers or users within your organization.
Recommended settings
User & Browser settings
We recommend enabling some settings on the domain to prevent Users (students) from interfering with Shield and any extensions.
Enable these settings in Devices > Chrome > Settings > Users & browsers

Some of these settings are mandatory.
Apps and Extensions
On the above-selected page, scroll down and navigate to the Apps and Extensions area, find the Task Manager setting,s and switch it to Block users from ending processes with the Chrome Task Manager.
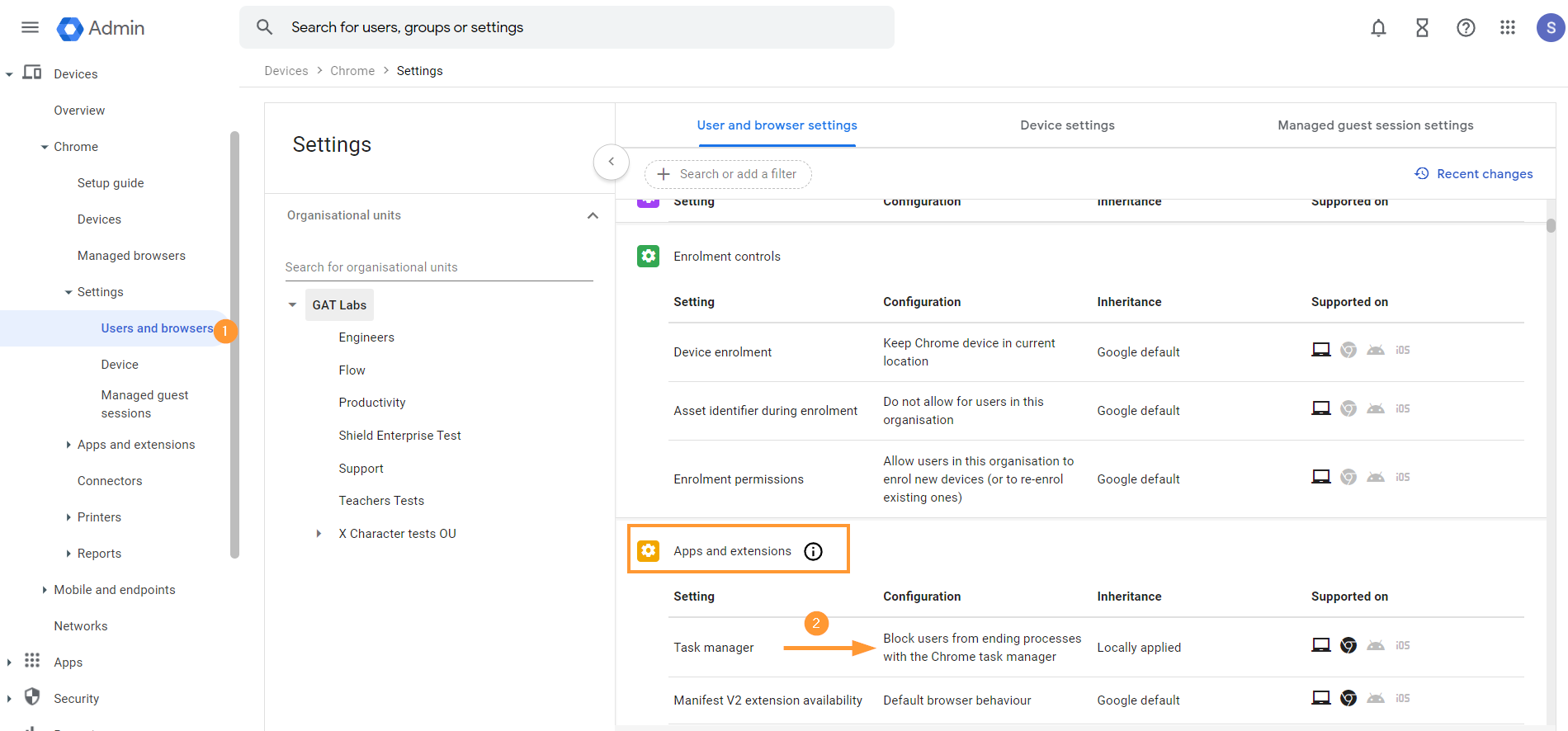
Description: Task Manager can be used to tamper with the Chrome browser’s normal operations.
User experience
On the same page, scroll down to User Experience
User & Browser settings > User Experience
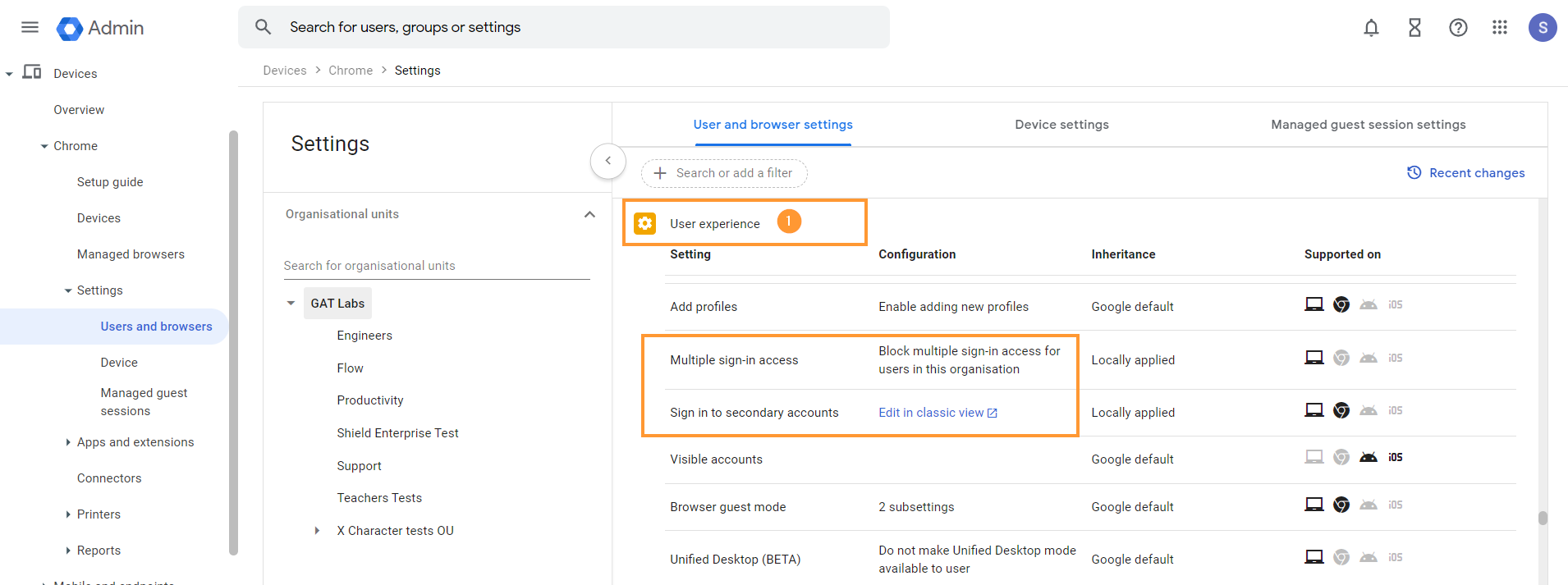
The following settings are highly recommended for schools using enrolled Chromebooks.
These settings prevent students from bypassing the network firewall and installing Android apps like VPNs and other web browsers on their Chromebooks.
- Multiple Sign-in access – Block multiple sign-in access for users in this organization
- Sign in to secondary accounts – Block users from signing in to or out of secondary Google accounts
In User experience, scroll also to Developer tools and set it to “Never allow use of built-in developer tools”

Description: Developer tools can be used to disable extensions. Google also recommends disabling these tools in most cases.
Security
The following three options are recommended for schools with enrolled Chromebooks. These settings prevent students from bypassing or tampering with the GAT Shield extension.
Scroll down to the Security tab
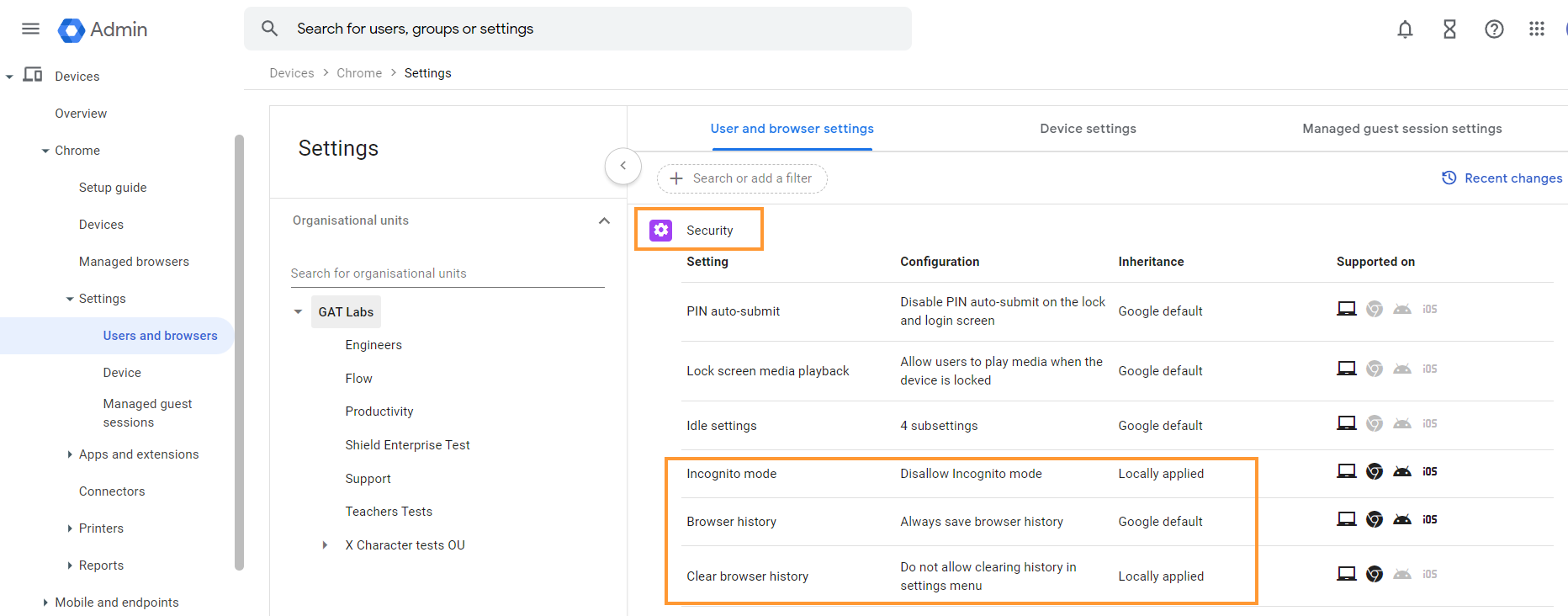
Find and apply the settings
- Incognito Mode – Disallow Incognito mode.
- Description: In incognito mode, the extensions do not work
- Browser history – Always save browser history.
- Description: Saving browser history is recommended so that when incidents occur, there is an audit trail that can be investigated by staff members.
- Clear Browser History – Do not allow clearing history in the settings menu.
- Description: The ability to clear browser history on the Chrome Browser may allow users to tamper with GAT Shield Browser reporting features.
Content
Scroll down further to the Content tab
- Screenshot – set it to Allow users to take screenshots.
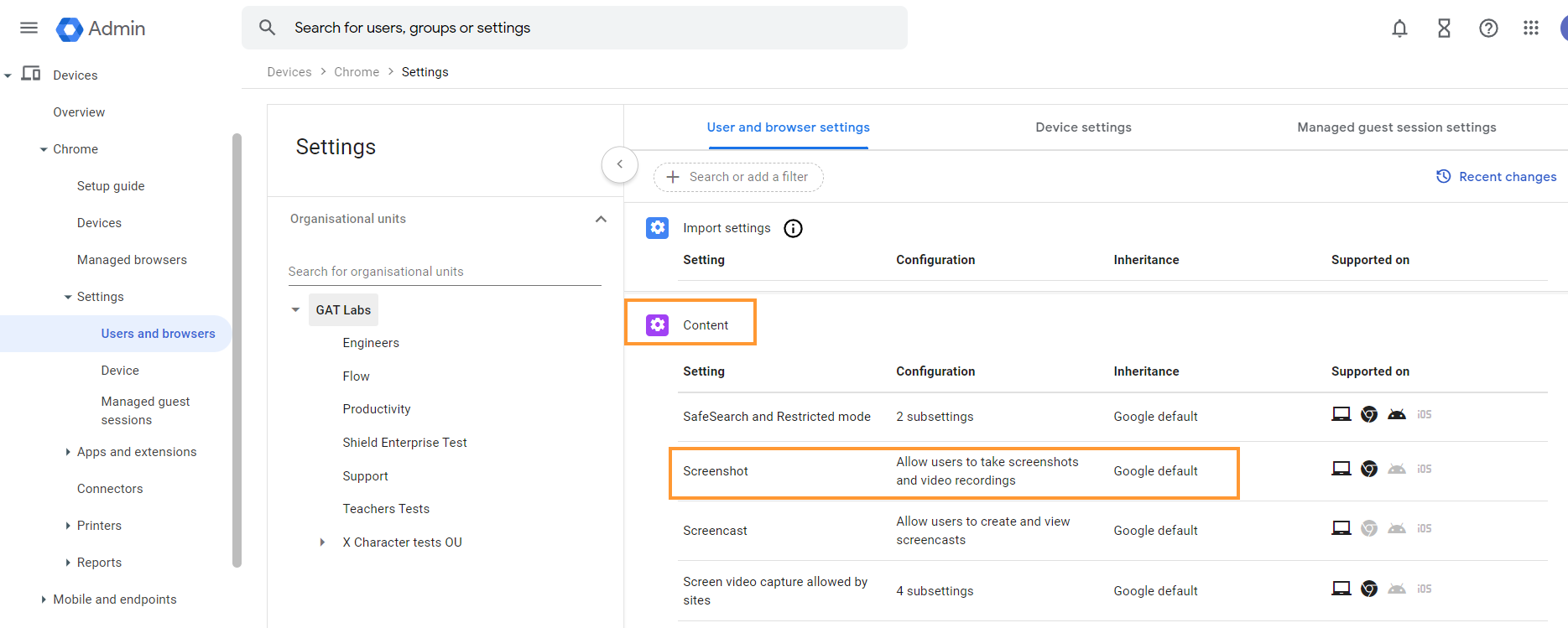
Description: Disabling screenshots will cause problems with the GAT Shield Alerting functionality.
When all of the settings are set up, make sure they are saved by clicking on the “Save” button on the top right.
Configure Device Settings
We recommend that these options be configured on your domain for your Chrome devices. Not all are mandatory.
From the Google Admin console, navigate to.
Devices > Chrome > Settings > Devices

In the left sidebar, select the OU that contains your Chromebooks, then configure the following policies to match these values.
Enrollment and access
- Configure the Enrollment and access
- Set Forced re-enrollment – automatically re-enroll after a wipe
- Set Verified access to Enable for content protection.
- Set Verified mode to require verified mode boot for verified access.

Sign-in settings
On the same page, scroll down to Sign-in settings
- Guest mode – Disable guest mode
- Sign-in restrictions – Restrict sign-in to a list of users
- Add an allowed list
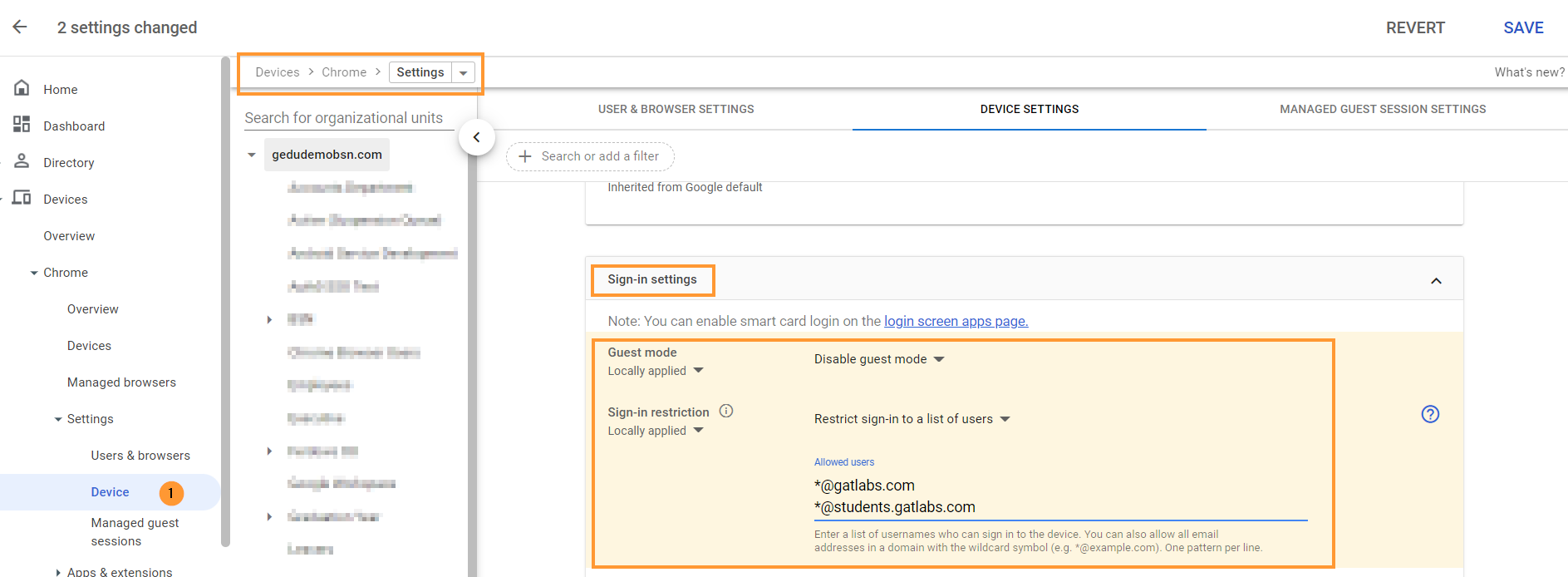
When done with the changes, click on the “Save” button on the top right.
Shield is deployed to all, but only ChromeOS devices are seen?
It could be a case where Shield is deployed domain-wide to all users, and yet the data is only shown on ChromeOS devices. You can check this setting.
Adjust the settings for Chrome management for signed-in users
Navigate to Devices > Chrome > Settings > Users and browsers > Chrome management for signed-in users

Set it up to: Apply all user policies when users sign in to Chrome, and provide a managed Chrome experience.
Referring to: Manage user profiles on Chrome browser, and View and configure apps and extensions
When the Shield extension is deployed, every user who logs into their Chrome Browser with their domain credentials will have the extension automatically synchronized.
The Chrome user cannot override this setting.
WebCam capture – Extension URL
If you wish to capture webcam images when Shield rules are triggered, then you will need to enable Video-input-allowed URLs and add the Shield URLs
This setting can be enabled in Devices > Chrome > Settings > Users & browsers
Then scroll down and navigate to Hardware, then to Video-input-allowed URLs

Add the WebCam URL, then click Save on the top right.
The unique ID and URLs are displayed in the GAT Shield Console – see below (GAT Shield extension ID and URL)
Remove the old WebCam extension
The old Webcam extension is no longer needed. Please remove
- webcamID: lncmmomdcmcilmblgmnlinenbinjklgg
Find the extension above and remove
GAT Shield Extension ID and URL
The GAT Shield extension ID and URL information are displayed in the GAT Shield Console that is launched from GAT+
See instructions below
Launch GAT+ on the top left, click on the GAT+ icon, a menu will be displayed – then select GAT Shield
To access and view the Extension ID and URL, navigate to GAT Shield > Configuration > Extension deployment.
Allow GAT Shield Extension via Firewall
Note: Depending on your Firewall setup, there might be restrictions set up and not allow traffic to Shield.
Please check your Firewall settings and allow the following URLs:
To install the extension, you need to whitelist the following domain: https://extension.gattool.com
Additionally need to whitelist domains based on region.
For US (Global) domains (no prefix) – US (default) region
- https://alert-shield.generalaudittool.com
- https://urlaccess-shield.generalaudittool.com
- https://activeid.generalaudittool.com
- https://shield.generalaudittool.com
For EU domains (eu-prefix) – EU region
- https://eu-alert-shield.generalaudittool.com
- https://eu-urlaccess-shield.generalaudittool.com
- https://eu-activeid.generalaudittool.com
- https://eu-shield.generalaudittool.com
Lastly, for UK domains (uk- prefix) – UK region
- https://uk-alert-shield.generalaudittool.com
- https://uk-urlaccess-shield.generalaudittool.com
- https://uk-activeid.generalaudittool.com
- https://uk-shield.generalaudittool.com
These URLs must be reachable and not blocked by the Firewall.
Force Install Extension Org Unit inheritance explained
Note: If you install Shield on “sub.. ou”, make sure it is – ‘Force install Inherited from the domain‘.
You can click on the extension ID, select “Force install,” and Save.
When it is set up as ‘Default – Inherited from Google default‘, Shield might not be active on the selected OU.
Finally, displaying Serial Numbers within the GAT Shield Console is available only for licensed enterprise-enrolled devices.
How to Install the New GAT Shield MV3 Extension
See Details
In this document, we will cover the steps to install the GAT Shield extension. It’s an audit, reporting, and security Chrome Extension for your Google Workspace environment.
Google Changes to Chrome
This June 2024, Google is making major changes to Chrome. They are moving from a standard called Manifest Version 2 (MV2) to one called Manifest Version 3 (MV3). These changes are major architectural changes that Google says will improve performance and security.
GAT Labs has been preparing for these changes for the last 2 years. This change is mandatory and will affect nearly all extensions that are deeply integrated with Chrome, including GAT Shield.
What does this mean for GATShield customers?
Firstly, and this is unavoidable, you will have to deploy a new version of GAT Shield.
We are making this process as seamless as possible and are providing a migration tool to help you move any configuration you may have in your existing GAT Shield to the new GAT Shield.
Install GAT Shield – MV3 extension
GAT Shield is a Chrome extension that the Super Admin of the domain must install via the Google Admin console. Below, we will cover how to deploy the GAT Shield extension to your users.
Step 1.
First, navigate to the Google Admin console.
In the Admin console, from the menu on the left, click on Devices > Chrome > Apps and extensions.
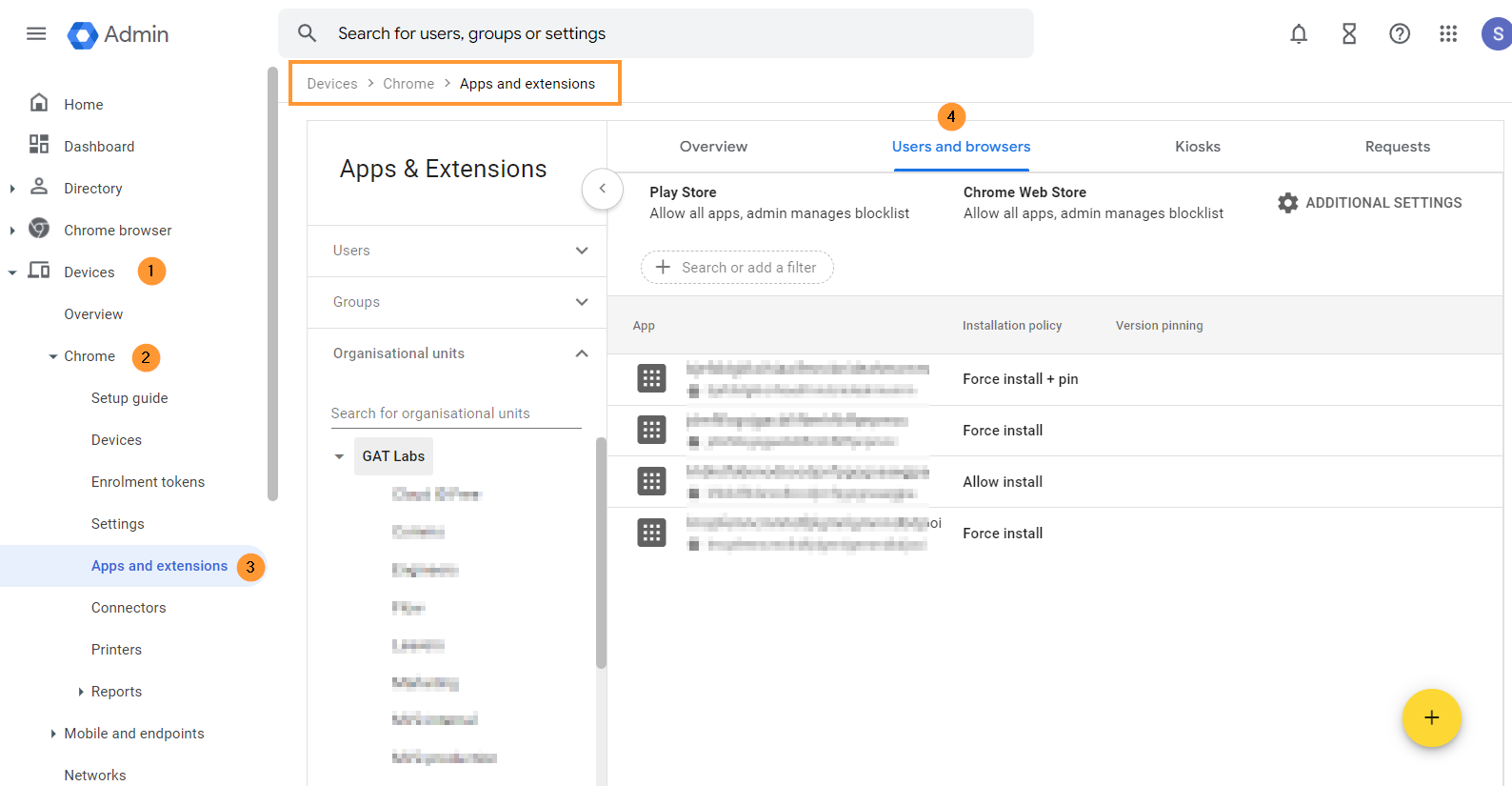
From the top menu, select Users and browsers.
A new page will be displayed with all the Chrome extensions deployed to the domain.
Step 2.
To install the GAT Shield extension, choose the root Org Unit (1) or a sub-OU where you want to deploy Shield (2).
On the bottom right side, click on the Yellow (+) button.

From the options shown, select Add the Chrome app or extension by ID (3).
Step 3.
Then, you will see a pop-up window. Select the From a custom URL option (1).
You can find the ID, URL, Webcam URL, and Policy for an extension in Shield under Help – Extensions deployment.
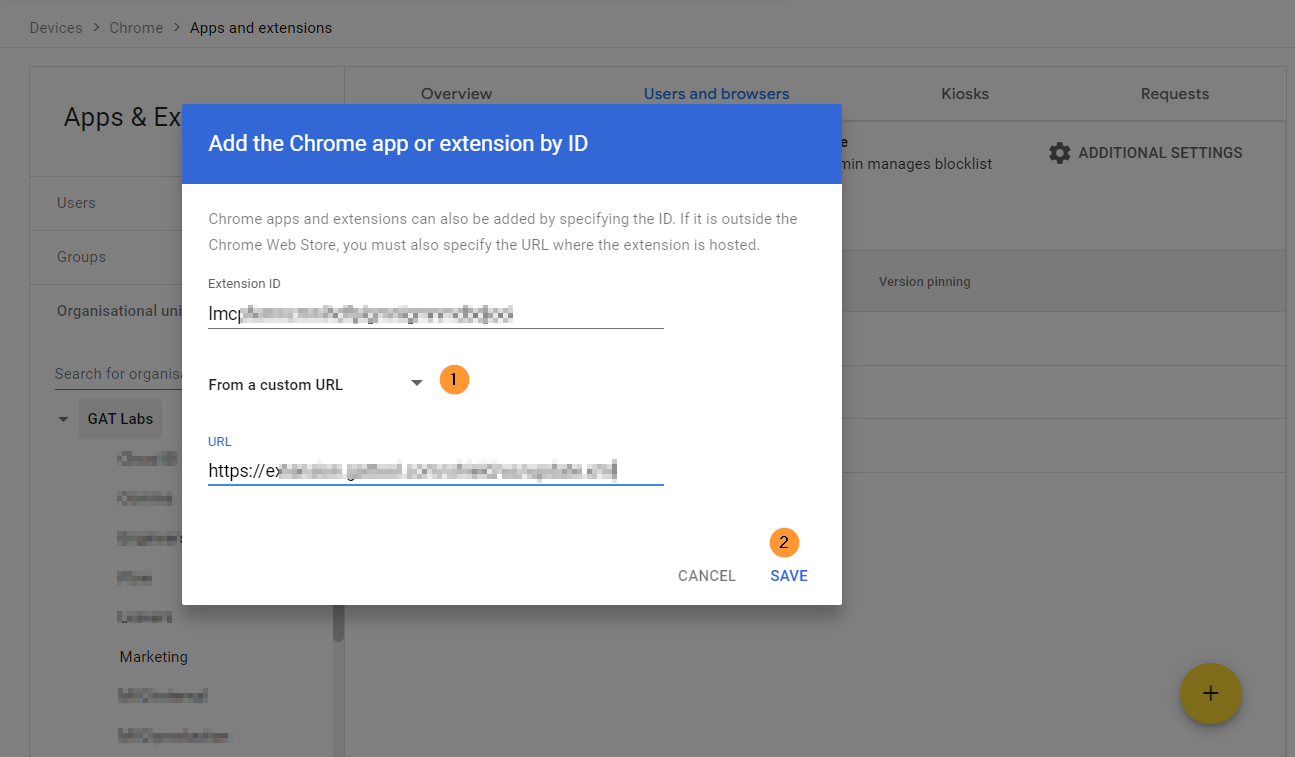
Click Save.
The Shield Extension is now installed.
Step 4.
Click on the newly installed extension. You will see a pop-up window on the side. In the Installation policy, click and select Force install.

Scroll down on the same window to the bottom of the page to find the Policy for extensions.

To access and view the Security Key, navigate to GAT Shield > Configuration > Extension deployment.
Under the Permissions and URL access field, click on and select Allow all permissions (2).

After doing all the changes, click the Save button on the top right.
Step 5.
To access and view the Extension ID and URL, navigate to GAT Shield > Configuration > Extension deployment.
Copy the ID, URL, Webcam URL, and Policy for an extension from here and use them in the Google Admin Console
Sentential One users see Note 1
Result
When the Shield extension is deployed, the end-users must be logged into the Google Chrome browser with their domain accounts.
The extension will appear under their Google extensions.
The browsing activity will then be reported to the GAT Shield console for the Admins to manage.
Note 1
Note that SentinelOne Antivirus blocks access to the GAT Shield plugin. To solve the problem related to that, uncheck the box – visible in Deep visibility, in the SentinelOne console:

Related Posts
How to Remove GAT Shield Extension
See Details
What happens when your GAT Shield license expires?
GAT Shield consists of two components: the GAT Shield Console and the GAT Shield extension.
If your trial license expires or your paid license is discontinued, we recommend removing the GAT Shield extension from all locations where it was deployed.
Remove the Extension
Log in to Google Admin Console as a Super Admin.
Navigate to Devices > Chrome > Apps & Extensions > Users & browsers > Overview

In the Overview tab – search for ID – enter a few letters of the Shield ID and Apply.
The result will show all the organization units where this extension is installed.

You can systematically remove it from each Org Unit if you have identified where the GAT Shield extension is deployed.
Clicking on the extension ID (2) – will display the extension details.
Click on the “bin icon” (3) – it will remove the app from the current org. unit.
NOTE: This must be done on each of the Org. Units where Shield is deployed, as it could be individually deployed to OUs and not inherited from the top OU etc.

Result
The Shield extension will be removed from your domain org. units and your end-users.
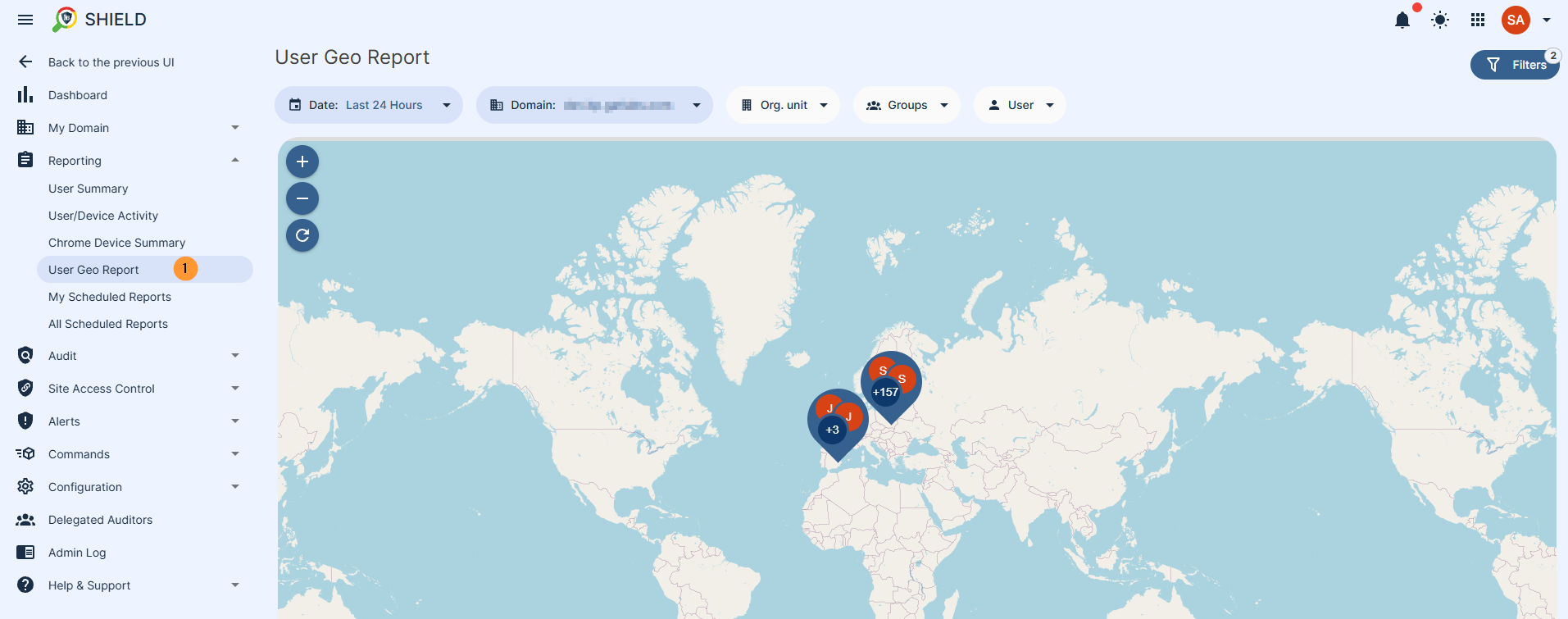
How does Geolocation in GAT Shield Work?
See Details
Our first go-to place to get the information is from the browser.
The location is given to the browser by Google, which utilises a variety of methods to determine the location. These methods are based on the WiFi hotspots the device sees.
Google learns this either from mobile devices that have geolocation enabled and are seeing WiFi hotspots or through the Google mapping cars that drive around, picking up WiFi hotspots and matching them to GPS data in the car.
With this guide you can quickly familiarise yourself with our products, making the most out of their powerful features to audit, secure and automate your Google Workspace domain.
If you’d like a detailed overview or require assistance, feel free to contact us at support@generalaudittool.com.

